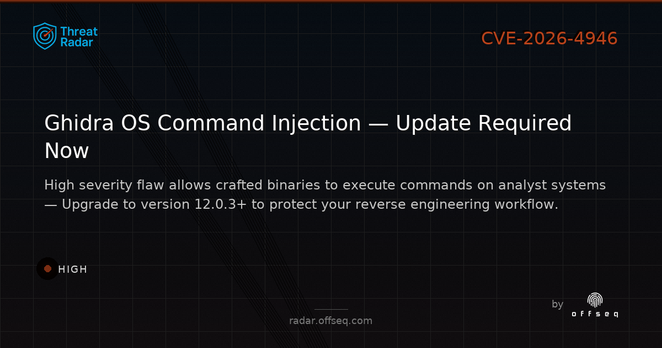
🛑 CVE-2026-4946: HIGH severity OS command injection in Ghidra <12.0.3. Crafted binaries can trigger arbitrary code via clickable @Execute annotations in the UI. Upgrade now & analyze unknown files in sandboxes. https://radar.offseq.com/threat/cve-2026-4946-cwe-78-improper-neutralization-of-sp-c53cae64 #OffSeq #Ghidra #BlueTeam
| Website | https://offseq.com |
| Threat Radar | https://radar.offseq.com |
| Guard | https://guard.offseq.com |
| Breach | https://breach.offseq.com |
| Training & Certifications | https://training.offseq.com |