| https://twitter.com/0x6d69636b | |
| GitHub | https://github.com/0x6d69636b |
| Location | Winterthur, Switzerland |
| Company | https://www.scip.ch/en/?team.misc |
Michael Schneider
- 166 Followers
- 164 Following
- 181 Posts
@tiraniddo
Yeah, the gist is:
Proc42_ServerMpUpdateEngineSignaturetriggers a Defender update, using a user-specified directory.- Download and unpack a real Defender update
- Force Defender to scan a file (EICAR)
- Use an oplock to freeze Defender
- Swap out the directory with a junction to
\BaseNamedObjects\Restricted
Because of the swap, Defender (running with privileges) operates on <updatepath>\mpasbase.vdm, which actually is \BaseNamedObjects\Restricted\mpasbase.vdm, which actually is \Device\HarddiskVolumeShadowCopyX\Windows\System32\config\SAM
Because Defender opens said file with a "Read" share mode, and it (the target) is in the object manager namespace, as opposed to NTFS, the unprivileged PoC process can read the file. Which is the SAM.
So basically a TOCTOU, with a bit of directory/junction shenanigans thrown in.
At least, that's my take on it.
🆕 New blog post!
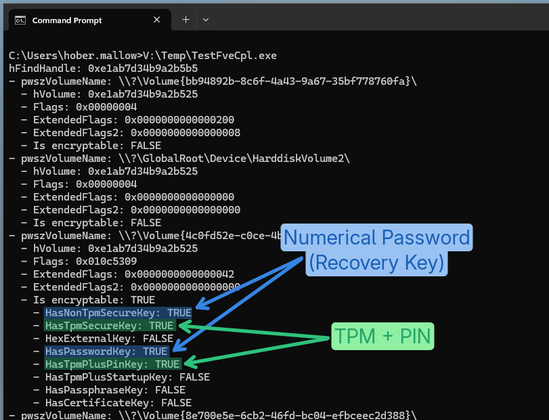
"BitLocker's Little Secrets: The Undocumented FVE API"
A small Windows RE adventure to figure out how to get the status and configuration of a BitLocker protected drive programmatically and without admin privileges.
Now also implemented in PrivescCheck! 🔥
👉 https://itm4n.github.io/bitlocker-little-secrets-the-undocumented-fve-api/
Yet another abuse of the missing "CrossDevice.Streaming.Source.dll" DLL!
After CVE-2025-24076 / CVE-2025-24076 found by Compass Security, Researcher Oscar Zanotti Campo found another vulnerability that he could exploit using the built-in misconfigured COM class referencing this DLL. This is CVE-2026-21508. 🔥
👉 https://0xc4r.github.io/posts/CVE-2026-21508/
👉 https://github.com/0xc4r/CVE-2026-21508_POC/
👉 https://blog.0patch.com/2026/03/micropatches-released-for-windows.html
RE: https://infosec.exchange/@enablesecurity/116300709031150946
VoIP/WebRTC security has needed a DVWA equivalent for a long time. We built DVRTC: full dockerized VoIP stack, intentionally vulnerable, 7 guided exercises.
Live instance at pbx1.dvrtc.net — try it now.
https://www.enablesecurity.com/blog/introducing-dvrtc-damn-vulnerable-real-time-communications/
#infosec #webrtc #voipsecurity #penetrationtesting #training
We found that Wi-Fi client isolation can often be bypassed. This allows an attacker who can connect to a network, either as a malicious insider or by connecting to a co-located open network, to attack others.
NDSS'26 paper: https://www.ndss-symposium.org/wp-content/uploads/2026-f1282-paper.pdf
GitHub: https://github.com/vanhoefm/airsnitch
High-level article on the work by Dan Goodin: https://arstechnica.com/security/2026/02/new-airsnitch-attack-breaks-wi-fi-encryption-in-homes-offices-and-enterprises/ I'd say we bypass Wi-Fi encryption though, in the sense that we can bypass client isolation. We don't break Wi-Fi authentication or encryption. Crypto is often bypassed instead of broken. And we bypass it ;) If you don't rely on client/network isolation, you are safe: we can't just break any Wi-Fi network.
New AirSnitch attack breaks Wi-Fi encryption in homes, offices, and enterprises: https://arstechnica.com/security/2026/02/new-airsnitch-attack-breaks-wi-fi-encryption-in-homes-offices-and-enterprises/
AirSnitch resets WiFi security back to the bad-old-days of ARP spoofing and trivial MITM.

GitHub - xchwarze/Cain: Password recovery tool for Microsoft Operating Systems. It allows easy recovery of various kind of passwords by sniffing the network, cracking encrypted passwords using Dictionary, Brute-Force and Cryptanalysis attacks and more!
Password recovery tool for Microsoft Operating Systems. It allows easy recovery of various kind of passwords by sniffing the network, cracking encrypted passwords using Dictionary, Brute-Force and ...