| Website | https://maxkersten.nl/ |
| https://twitter.com/Libranalysis |
Max 'Libra' Kersten
- 156 Followers
- 41 Following
- 19 Posts
Rhysida Ransomware
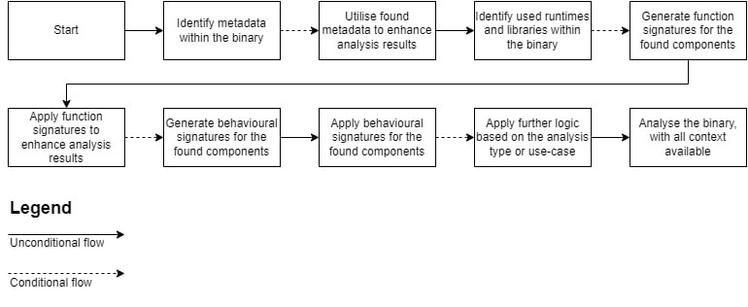
New ransomware victims are made every day by ransom gangs with a variety of ransomware malware families, one of which is the Rhysida ransomware family. Within this blog, an anonymised version of an attack by the Rhysida ransom operators is examined, along with a technical deep dive into the ransomware itself. The main purpose of this blog is to raise the bar for defenders by detailing the malware operator’s techniques. By sharing factual observations, along with our additional insights, regardless of the security products in use, one can improve their security posture. Although the steps an actor takes might occur in a short time span, one can create additional and granular detection rules for the steps listed in this blog.
Shining Light on Dark Power: Yet Another Ransomware Gang
Another day, another ransomware gang. The Dark Power ransomware gang is new on the block, and is trying to make a name for itself. This blog dives into the specifics of the ransomware used by the gang, as well as some information regarding their victim naming and shaming website, filled with non-paying victims and stolen data.
Ever wondered how API hashing in malware works, how to deal with it with as little as possible? In my latest addition to my Binary Analysis Course, I've written extensively about this: https://maxkersten.nl/binary-analysis-course/malware-snippets/plugxs-api-hashing/
This blog refers to @herrcore's HashDB, for which a pull-request is pending with the given PlugX hashing algorithm. Thank you for creating and maintaining such a platform!
https://www.botconf.eu/botconf-2023/botconf-2023-schedule/
As part of a new chapter of my Binary Analysis Course, snippets from malware samples are examined in great detail, all in my signature step-by-step analysis method. This article goes into great detail with regards to the self deletion of a sample, and how the malware avoids deleting a file that is in-use: https://maxkersten.nl/binary-analysis-course/malware-snippets/self-deletion/
It's going to be another amazing edition!
The #Botconf2023 programme committee is busy reviewing this year's submissions... Plenty ! Thanks to all authors !
We plan on advising authors on January 15th and will start publishing the programme as soon as each of the accepted talks accept.
The registrations for this year should open about the same day. Please except a slight increase in tariffs for your participation fees as our costs have increased this year, like everyone's.
In Kaspersky's recent post about Ghidra (more here: https://securelist.com/how-to-train-your-ghidra/108272/) Function ID databases for VS2013 and Delphi were included, although it seems like this has been missed by many, so here is a friendly reminder.
The direct URL to the FIDBs: https://media.kasperskycontenthub.com/wp-content/uploads/sites/43/2022/12/fidbs_typeinfo.7z