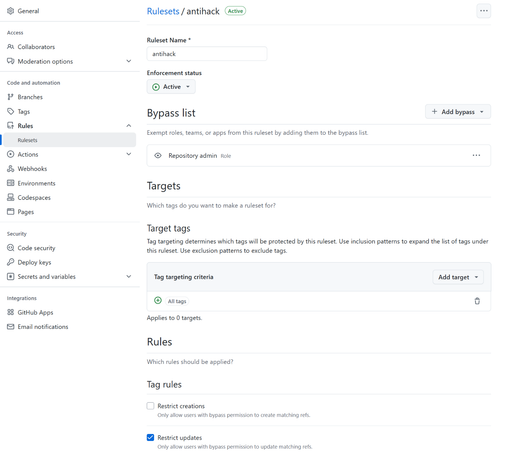
I have a feeling CVE-2025-30066 could have been prevented if the "tj-actions/changed-files" had the repository tag protection setting and the stolen PAT wasn't overprivileged.
Jaroslav Lobačevski 🇺🇦 🇱🇹
- 54 Followers
- 84 Following
- 17 Posts
OpenAI (Open-source Application Insecurity) Researcher at GitHub Security Lab. Opinions are my own. Russian warship go http://f.ck yourself.
I made a thing... or two. GitHub Actions permissions Monitor and Advisor: #GitHubActions #security
I am glad to share that CVE-2022-23529 has been withdrawn - there is no room to escape if the attacker already controls the object in memory, even in the latest version of jsonwebtoken library: