it's a interesting world we live in where the rewrite-in-rust army has now gotten nuclear weapons in the form of LLM's, and they are not afraid to use them :-D
The backstory for why I started thinking about this is that CIRCL.lu runs this vulnerability-lookup project, which is great. But I had some ideas how to improve the notification emails so I wanted to look into what it would need to self-host in order to customise it for my use.
But I got distracted by this, I rewrote it in rust, issue.
Someone just had a LLM reimplement everything in rust, I think in order to reduce the system requirements for running the project.
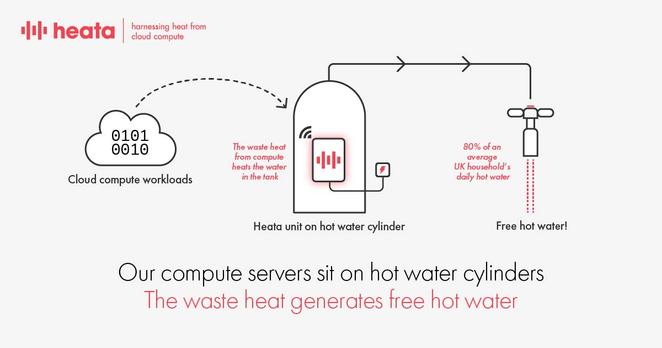
I mean, I'm very divided. I love efficient computing. I am not going to (want to) self-host vulnerability-lookup if it needs 7 different services and 16 GiBs of RAM. So a efficient rust implementation would be interesting.
But after looking at the code, I am not sure this is the right approach. I told codex to look at it before deploying it and there are so much unnecessary stuff in there. Is it slop? I don't know, I guess that depends if someone keeps maintaining and improving it for more than a month.
Just because you can does not mean you should.
Would it have been better to take those tokens and spend it on improving the slow or resource intensive parts of the original project?