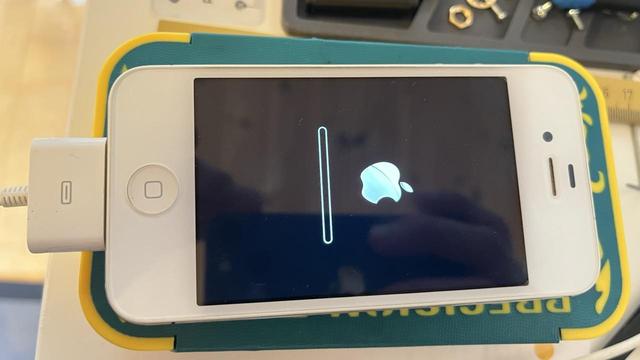
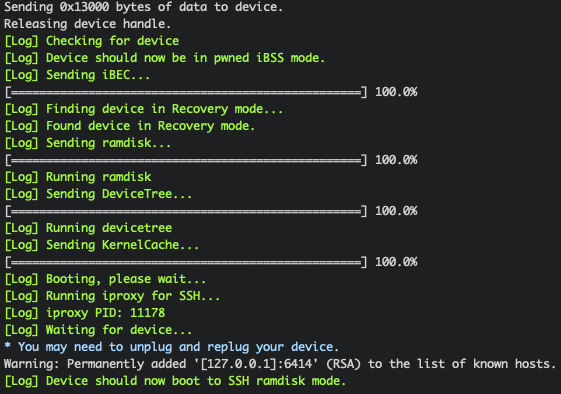
Doing some iPhone 4S forensics today, first time using checkm8 , had to get a Pi Pico because the 4S is picky about its exploits.
But lo and behold, we have ssh ramdisk.
So... Gabriel, why would you be doing iPhone forensics? I guess there must be something really valuable on that 4S?
Yeah.... about that..
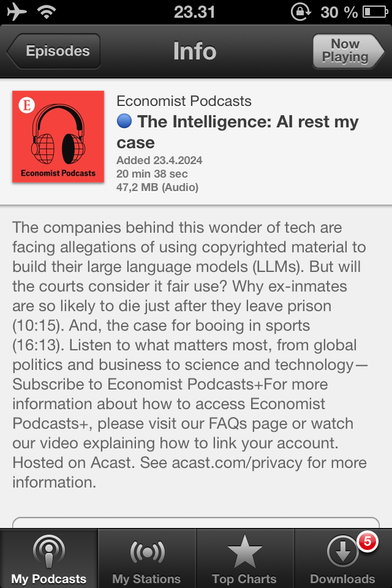
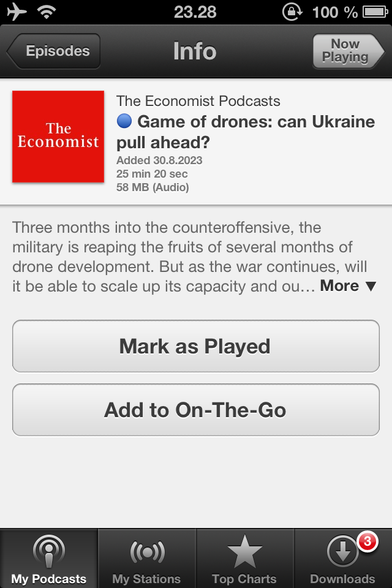
It might have been just my collection of Economist podcast pun's.... also I liked this device.
My last pre-flat device so I wanted to rescue it, and some jailbreak had caused it to go into a boot-loop.