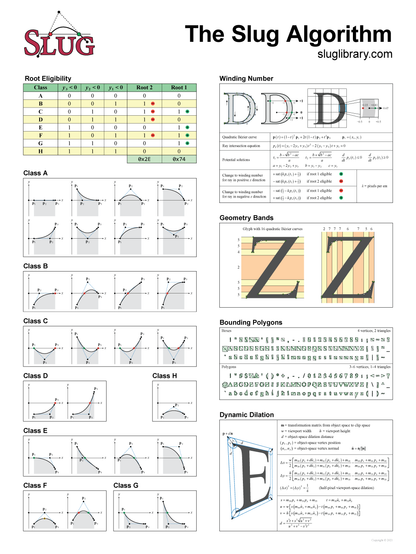
New blog post: A Decade of Slug
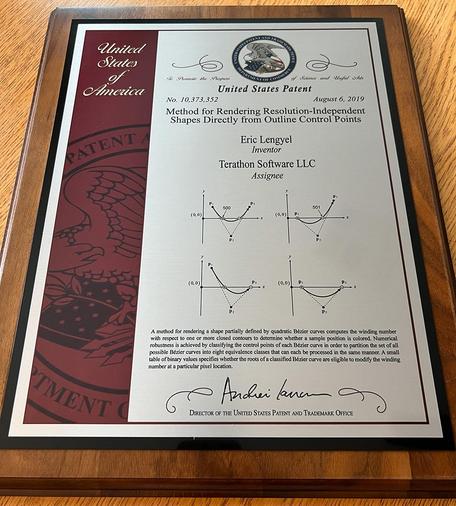
This talks about the evolution of the Slug font rendering algorithm, and it includes an exciting announcement: The patent has been dedicated to the public domain.
https://terathon.com/blog/decade-slug.html
This talks about the evolution of the Slug font rendering algorithm, and it includes an exciting announcement: The patent has been dedicated to the public domain.
https://terathon.com/blog/decade-slug.html