| Website | https://dimitrifourny.github.io |
| https://twitter.com/DimitriFourny |
Dimitri Fourny
- 154 Followers
- 68 Following
- 53 Posts
Extracting liblockdown.dylib from visionOS dyld shared cache and running it
with a DBI on macOS?
Challenge accepted!
📖 Blog: https://www.romainthomas.fr/post/24-09-apple-lockdown-dbi-lifting/
🎞️ Demo: https://www.youtube.com/watch?v=5L05OE5mL2o
⌨️ Code: https://github.com/romainthomas/visionOS-liblockdown
Interested in decompiler design? You'll love our latest blog post! https://binary.ninja/2024/06/19/restructuring-the-decompiler.html
Not interested? You'll still love the massive improvements the latest update brings to control flow recovery! Simpler conditionals, flatter code depth, more accurate transformations, easier to read and understand. Everything is better.
https://googleprojectzero.blogspot.com/2024/06/project-naptime.html
Finally got around to publishing the slides of my OffensiveCon talk from ~two weeks ago. Sorry for the delay!
The V8 Heap Sandbox: https://saelo.github.io/presentations/offensivecon_24_the_v8_heap_sandbox.pdf
Fantastic conference, as usual! :)
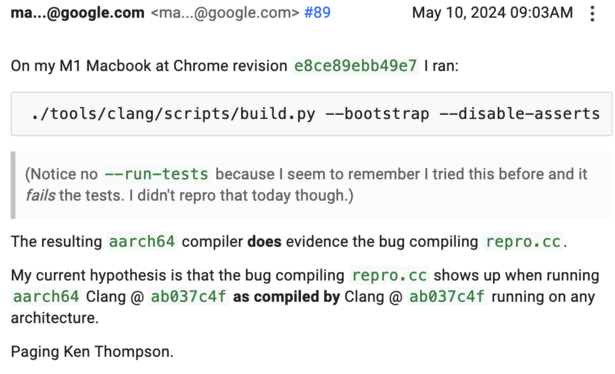
I've found compiler bugs before, but this is the first compiler-compiler bug I've ever seen – incredible stuff:
Big day for the V8 Sandbox:
* Now included in the Chrome VRP: http://g.co/chrome/vrp/#v8-sandbox-bypass-rewards
* Motivation & goals discussed in a new technical blog post: http://v8.dev/blog/sandbox
If there is ever a Sandbox "beta" release, this is it!
I ported my kernel dump parser library to Rust; go give it a try! 🦀