David Agranovich 

- 585 Followers
- 161 Following
- 26 Posts
A quick example of why ADS-B is really important, from the perspective of someone who spends a lot of time in extremely busy, congested airspace, often doing unpredictable stuff.
Most smaller (non-airline) planes today use ADSB for traffic deconfliction, and it’s been a huge, affordable improvement for safety in congested airspace. I have a $50 Linux home built ADSB receiver I use with students, and it’s helped us avoid dangerous situations like this F-18 on a Bay Tour.
It's the end of the year, which means it's time to post a threat report (or three)! Our team just shared three reports based on our threat research into influence operations and cyber-espionage activity over the past year.
🫡 Lookback at 200+ CIB disruptions: https://about.fb.com/news/2022/12/metas-2022-coordinated-inauthentic-behavior-enforcements/
🕵️♂️ Surveillance-for-Hire investigations: https://about.fb.com/wp-content/uploads/2022/12/Threat-Report-on-the-Surveillance-for-Hire-Industry.pdf
👨⚖️ Policy recs to tackle the surveillance industry: https://about.fb.com/wp-content/uploads/2022/12/Meta-Policy-Recommendations-for-Tackling-the-Surveillance-for-Hire-Industry.pdf
First, these reports show how we’ve expanded the adversarial threat disruption model since 2017 to multiple threats: influence ops, cyber-espionage, surveillance, spam, scams, etc. We’ve now taken down more than 200 CIB networks globally - and fittingly, our first and 200th takedown were both info ops from Russia.
That said, our work to counter these threats is global - we’ve disrupted IO from 68 countries in more than 42 languages (cool map attached)
You can read about these cases in our new Security Center, which houses our investigative reports and deep dives into threat disruptions, in chronological order: https://transparency.fb.com/metasecurity/threat-reporting
Our surveillance-for-hire report focuses on new entities engaged in recon, engagement, or exploitation on behalf of clients around the world, building on our last year’s report. Key takeaway: this industry is much more than 1-2 firms, so requires a comprehensive society-wide response.
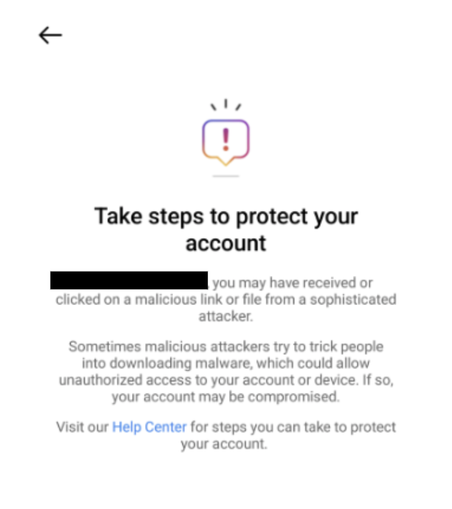
Claims these firms only target terrorists and criminals just don’t hold water. We continue to see indiscriminate targeting of journalists, dissidents, and businesses. We alerted people we believe were targeted, and provided specific steps to help protect their presence online (example of notifs also attached).
We’ve seen surveillance actors aggressively try to reconstitute and target people across the internet, highlighting the need for a more holistic response to constrain abusive behavior. To that end, we published recs for gov, civil society, and industry to tackle the problem. Link here: https://about.fb.com/wp-content/uploads/2022/12/Meta-Policy-Recommendations-for-Tackling-the-Surveillance-for-Hire-Industry.pdf
There are many important recommendations, so definitely read the paper, but three key ones I want to call out:
1. Demand for these tools invites abuse. Governments should restrict, or in some cases, ban, the sale of spyware and malware, and commit to not purchasing these capabilities. https://www.nytimes.com/2022/11/12/us/politics/fbi-pegasus-spyware-phones-nso.html
2. Impunity enables bad behavior. Governments and regulators should consider leveraging sanctions (incl. Magnitsky Act) to hold surveillance-for-hire companies accountable when they sell tools to indiscriminately target people https://www.wyden.senate.gov/imo/media/doc/Global%20Magnitsky%20Sanctions%20Letter%20to%20Sec.%20Yellen%20&%20Blinken.pdf
3. People often don’t know if they’ve been targeted and can't easily confirm suspicions. Govts should create accountability reqs for surveillance-for-hire companies, including notice to targeted individuals, and impose oversight to ensure compliance. https://citizenlab.ca/2021/12/pegasus-vs-predator-dissidents-doubly-infected-iphone-reveals-cytrox-mercenary-spyware/
Companies that indiscriminately sell surveillanceware democratize access to sophisticated hacking capabilities while obscuring the people behind their activity. This report, and collective effort from industry, gov, and civil society, can help shine a light on the darkness.