chrp chrp
- 25 Followers
- 343 Following
- 740 Posts
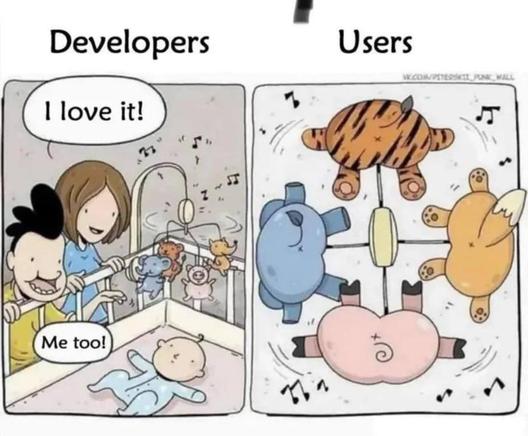
The old internet is still here, what's changed is our expectations. Some great positive thoughts this morning by @tylergaw
Ja dafür ist der Staat doch auch da. Dafür haben wir die Menschen im Staatsdienst angestellt. Dafür bekommen die unsere Stimmen und unser Geld. Wir bezahlen dafür, dass es im Alter eine Rente für uns gibt.
Die jungen Leute wachsen gerade mit dem Bewusstsein auf, dass "der Staat" eine vom Menschen abgekoppelte Instanz sei, die irgendwelchen Behördenkram für Großfirmen erledigt...
Wir müssen sehr sehr dringend den Sozialstaat wiederherstellen, bevor sich niemand mehr daran erinnern kann.
Static + dynamic analysis of Signal's APK. The good news first: Signal is genuinely exceptional.
Rust core (libsignal_jni.so), post-quantum hybrid Double Ratchet (Kyber-1024 + X25519), Direct ByteBuffers with immediate zeroing after PIN/username hashing, Intel SGX attestation for SVR — MREnclave verification means even a compromised Signal server can't extract your PIN hash.
But two things stood out:
1. Firebase is always there. Google receives IP + notification timestamps regardless of message content. If you need metadata privacy, Signal still leaks presence data to Google's infrastructure.
2. Certificate revocation endpoints hit http://g.symcd.com in plaintext. An ISP or state-level observer can fingerprint Signal usage from DNS queries and HTTP traffic to those CAs — without touching message content.
Conclusion: strongest crypto engineering in consumer messaging. The attack surface isn't the cryptography. It's the operational dependencies.
Soon the full analysis
#infosec #AndroidSecurity #Signal #privacy #ReverseEngineering #postquantum #mobileforensics
Mein Interview für die @AG_KRITIS bei DLF Hintergrund zu:
#Palantir in den USA: Ein Schreckensszenario für Deutschland?
"Um Migranten aufzuspüren, nutzt die US-Einwanderungsbehörde Software von Palantir. Das befeuert die Kritik an der Software, die auch in Deutschland zum Einsatz kommt – weil sie zwar umstritten ist, aber bei vielen Experten als unverzichtbar gilt."
https://www.deutschlandfunk.de/palantir-in-den-usa-ein-schreckensszenario-fuer-deutschland-100.html
elf Millionen Menschen ohne Strom