| Website | caitlincondon.com |
Caitlin Condon
- 1.3K Followers
- 711 Following
- 949 Posts
👋 There's been a lot of discussion recently about the volume of vulnerability reports that PSIRTs, open-source maintainers, and technology producers are receiving. The CVE Program's Researcher Working Group (RWG), which I've been chairing for the last 9 months, is developing guidance for security researchers on how to most effectively report new vulnerabilities to supplier organizations.
👉 We're seeking input from the community on the data points, report characteristics, and reporting practices that help reduce time-to-verification for new vulnerabilities. If you're a researcher, a PSIRT, a VM or SecOps practitioner, or a bug bounty provider who's been on the hook for looking at or validating vulnerability reports in your career, we want your feedback on what works — and what doesn't!
🗓️ The discussion will stay open through (at least) June 5, 2026. Feedback is best submitted by commenting on the GitHub issue below!
https://github.com/CVEProject/researcher-working-group/discussions/29
New list! 2026 routinely targeted vulnerabilities (so far)
https://www.vulncheck.com/blog/routinely-targeted-vulnerabilities-may-2026
👋 There's been a lot of discussion recently about the volume of vulnerability reports that PSIRTs, open-source maintainers, and technology producers are receiving. The CVE Program's Researcher Working Group (RWG), which I've been chairing for the last 9 months, is developing guidance for security researchers on how to most effectively report new vulnerabilities to supplier organizations.
👉 We're seeking input from the community on the data points, report characteristics, and reporting practices that help reduce time-to-verification for new vulnerabilities. If you're a researcher, a PSIRT, a VM or SecOps practitioner, or a bug bounty provider who's been on the hook for looking at or validating vulnerability reports in your career, we want your feedback on what works — and what doesn't!
🗓️ The discussion will stay open through (at least) June 5, 2026. Feedback is best submitted by commenting on the GitHub issue below!
https://github.com/CVEProject/researcher-working-group/discussions/29
"That's the dumbest shit I've read in a bit"
- Quote from the team exploit mines 2026-05-16T00:06:00Z
❗Earlier today, VulnCheck Canaries detected first-time exploitation of CVE-2026-28515 and CVE-2026-28517 in openDCIM, an open-source code base used for data center infrastructure management.
🐚 The cluster of attacker activity we're observing so far originates from a single Chinese IP and uses what appears to be a customized implementation of AI vuln discovery tool Vulnhuntr to automatically check for vulnerable installations before dropping a PHP webshell.
🌐 The VulnCheck team's ASM queries for these vulnerabilities find fewer than 50 systems online, many of which belong to higher education institutions globally. Both CVEs were discovered by new VulnCheck research team member @chocapikk_.
Moar KEVs: https://www.vulncheck.com/kev
Quote from the team exploit mines 2026-05-11T22:33:00Z:
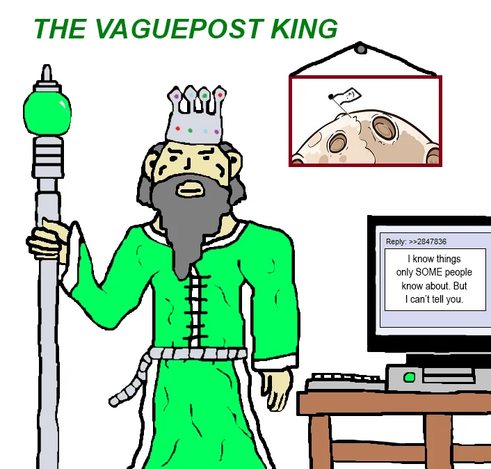
"Average vendor advisories when you're trying to find an INCH of context about vulnerabilities"