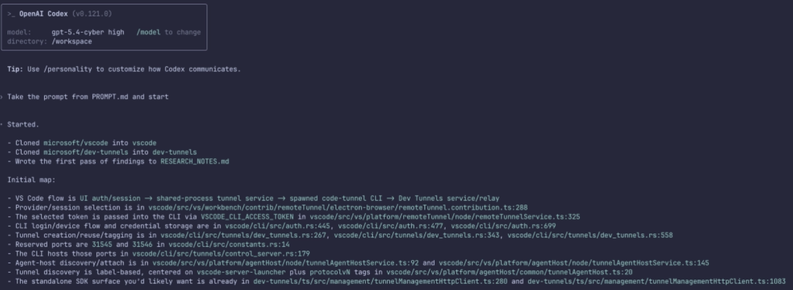
GOOGLE JUST SILENTLY DOWNLOADED A 4GB AI MODEL TO YOUR COMPUTER WITHOUT ASKING.. WITHOUT TELLING YOU.. AND WITHOUT ANY WAY TO STOP IT..
If you use Chrome.. There's a good chance a 4 gigabyte file is sitting on your hard drive right now that you never agreed to download..
It's called Gemini Nano.. Google's on-device AI model..
https://x.com/i/status/2051782956134592933

Evan Luthra (@EvanLuthra) on X
🚨GOOGLE JUST SILENTLY DOWNLOADED A 4GB AI MODEL TO YOUR COMPUTER WITHOUT ASKING.. WITHOUT TELLING YOU.. AND WITHOUT ANY WAY TO STOP IT.. If you use Chrome.. There's a good chance a 4 gigabyte file is sitting on your hard drive right now that you never agreed to download.. It's