"In particular, the RDP bitmap cache of the beachhead host shows the threat actor opening the Veeam Backup & Replication console."
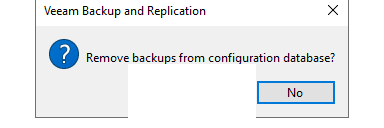
From there, they browsed active backup jobs, tape infrastructure, and storage repositories — before removing backups from the configuration database, as evidenced by reconstructed RDP bitmap cache artifacts.
Report: https://thedfirreport.com/2025/12/17/cats-got-your-files-lynx-ransomware/
Services: https://thedfirreport.com/services/
Contact Us for pricing or a demo: https://thedfirreport.com/contact/