End-to-end encryption doesn’t mean end-to-end protection.
Yes, WhatsApp encrypts your messages. But hackers don’t need to break the encryption.
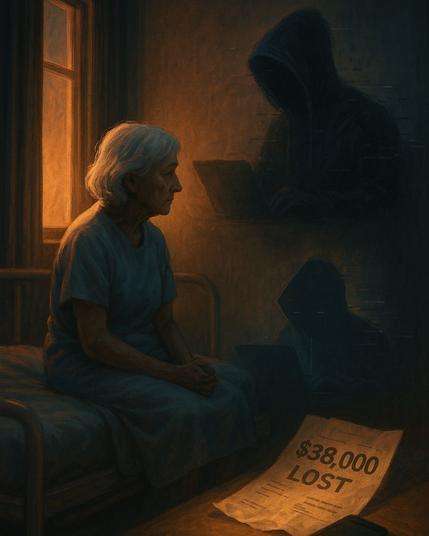
They just need to break you.
That’s how most attacks happen.
Not with code — with clever manipulation.
A fake support message.
A phishing link.
A friend’s hijacked account asking for a code.
And the real damage comes after:
- Access to your chats
- Identity theft via your photo, name, and contacts
- Password resets and account takeovers (thanks to 2FA tied to your number)
- SIM swap attacks that bypass your entire digital perimeter
What makes it worse?
Most users never touch their privacy settings.
They leave “Last Seen,” profile photo, and group invites open to everyone.
They don’t enable 2FA.
They don’t encrypt backups.
They don’t lock the app or check for spyware.
And then they’re shocked when everything unravels in hours.
WhatsApp gives you the tools — but they don’t turn them on for you.
Here are 8 settings you should activate today:
1. 2FA PIN
2. Profile visibility: Contacts only
3. Group invite restrictions
4. Security code change alerts
5. Biometric app lock
6. Disappearing messages
7. Encrypted backups
8. App updates to patch spyware exploits
Cybercriminals don’t break into accounts.
They walk right through the front door — because it’s usually wide open.
Your security is only as strong as the habits behind it.