Data can be encoded in anything that changes state — not just file content or network packets.
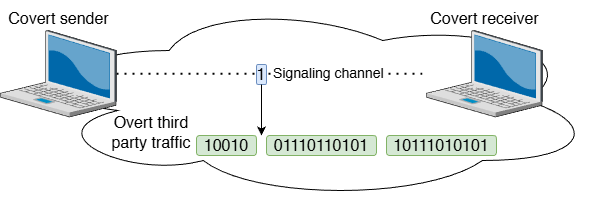
The principle of Covert Channel
In short, it's a communication path that was never intended to be used for communication. Instead of using a legitimate, observable channel, two parties encode information into some aspect of a system that changes state which both parties observe
Based on research, this dates back to a 1973 paper by Butler Lampson on the confinement problem. He described a scenario where a malicious process could leaf info to an outside observer not by writing files or opening sockets, but by modulating its own CPU usage mesured by the observer. Basically the observer doesn't read a message, it deducts one from a side effect.
Categories of Covert Channels
This broadly fall into two types
- Storage channels
- Timing channels
The first type encode data by modifying a "shared system attribute" that another process an read. File permissions, timestamps, process IDs, registery keys, and even the presence or absence of a file are all storage channels. The recent crackme challenge used a storage channel.
The receiver measures the gaps. CPU cache timing attacks like Spectre and Meltdown are timing channels operating at the nanosecond level.
In the recent crackme challenge, both binaries once executed only took about 1.3 seconds to communicate and end cleanly.
In order to intercept the communication (the goal), I had to set my python interceptor to use 1 Microsecond (0.00001 seconds) in order to not miss a single byte. Even that wasn't enough. I had to pause every process, program etc even network to avoid any form of interruption.
A real world example concerning convert channels involves the popular vulnerabilities; Spectre and Meltdown as mentioned previously
You can read more about them here
meltdownattack.com
I'll be going deeper into it (covert channels) as it really caught all my attention during the challenge. I'll write down a research doc on it. If I find something deeper, interesting and perhaps critical and worth reporting that'll be fantastic and worth the pursuit.