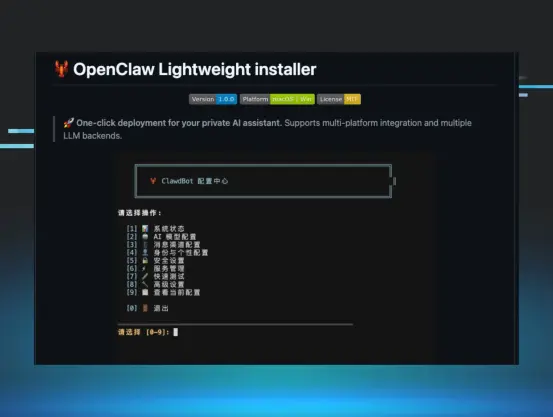
I teamed up with Ryan Dowd to investigate a fake OpenClaw installer hosted on GitHub. This was also picked up by Bing's AI and recommended as the correct way to install OpenClaw on Windows.
The executable had 0 VT hits, and the MacOS variant would deploy a binary likely to be Atomic MacOS Stealer. The executable didn't run in sandboxed environments, and was deploying information stealers in addition to GhostSocks.
The addition of GhostSocks is interesting as it turns compromised systems into a proxy the threat actor can use to route their logins through. This enables them to bypass anti-fraud checks from online services. It also contained a hidden parameter which if given would launch in a debugging mode providing complete insight into the GhostSocks configuration.
This is a current campaign impersonating popular GitHub repositories claiming to be easier methods of installation, and the threat actor is posting issues on legitimate GitHub projects to help drive traffic to their malicious repositories.
Have a read, hope you enjoy.
https://www.huntress.com/blog/openclaw-github-ghostsocks-infostealer