I block people who follow me & don’t post. I have two rescue Miniature Poodles.
Alida Antonia
- 114 Followers
- 469 Following
- 1,006 Posts
I block people who follow me & don’t post. I have two rescue Miniature Poodles.

Kevin Woods: Why Companies MUST Invest in Junior Cyber Talent - Phillip Wylie
Summary In this episode of the Phillip Wylie Show, Kevin Woods from GuidePoint Security shares his unique journey into cybersecurity, emphasizing the importance of community support, hands-on experience, and investing in entry-level talent. He discusses the various paths one can take in the cybersecurity field, the value of certifications, and the role of education in…
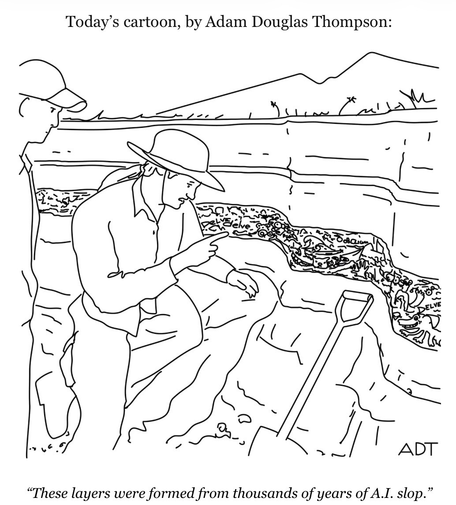
PSA: you can ignore the entirety of the LLM-industrial-complex without falling for the “see they are useful for something after all” narrative:
- these systems are based on theft (some of that still makes its way through the courts)
- they are designed to centralise power in the hands of very few people who are also objectively the worst people
- the businesses are not sustainable, nobody disagrees the bubble will pop before long, so making your craft depend on a subscription seems silly
Not surprised. Gift article. #bankrupties #Tariffs #trumpadministration
Been working on an important series of follow-up stories about the evolution of the Aisuru botnet, an Internet-of-Things (IoT) botnet that's been blamed for successive record-smashing DDoS attacks in recent months. Meanwhile, the people who have controlled Aisuru for some time recently insisted up and down that they were not responsible for the massive Aisuru attacks of late.
Hats off to Xlab for this incredible report, which explains (to a degree) how Aisuru gave rise to a distinct botnet called Kimwolf, which has an estimated 2-3 million infected hosts and is growing rapidly. I don't have to tell anyone that if 800k bots from Aisuru can down the largest sites on the internet, Kimwolf can take down entire countries.
https://blog.xlab.qianxin.com/p/13ae0f3c-a75d-4764-b8f2-37e14f976935/
史上最疯:独家揭秘感染全球180万Android设备的巨型僵尸网络Kimwolf
背景介绍 2025年10月24日,安全社区的信任伙伴给我们提供了一个全新的僵尸网络样本,该样本最特别的地方是它的C2域名14emeliaterracewestroxburyma02132[.]su彼时在Cloudflare 域名流行度排名中位列第2,一周之后甚至超越Google,问鼎Cloudflare 域名流行度排名全球第一。毫无疑问这是一个超级大规模的僵尸网络,基于样本运行时输出的信息以及使用wolfssl库,我们将它命名为Kimwolf. Kimwolf 是一个使用 NDK 编译的僵尸网络,除具备典型的 DDoS 攻击能力外,还集成了代理转发、反向 Shell 和文件管理等功能。从整体架构来看,其功能设计并不复杂,但其中仍有一些值得关注的亮点:例如,该样本采用了简单而有效的栈异或(Stack XOR)操作对敏感数据进行加密;同时利用 DNS over TLS(DoT)协议封装 DNS 请求,以规避传统安全检测。此外,其 C2 身份认证采用基于椭圆曲线的数字签名保护机制,Bot 端会在验签通过后才接受通信指令。近期更引入EtherHiding技术以区块链域名对抗处置,
RE: https://infosec.exchange/@BleepingComputer/115734914703339891
I wonder if this is why my son hasn’t answered my question, but he’s also busy herding cats. He has his own server.
This is a good thing, but it’s still more plastic in our blood.
#Apple #tech #packaging #business #madeintheUSA
#microplastics
https://www.wired.com/story/apple-manufacturing-academy-michigan/
Families sue #Al company for wrongful deaths.