I've been feeling very bad about cybersecurity as a career for a while now, and it's due to GenAI. It feels utterly hopeless fighting against the hype and fear. It fucking sucks, as it's not possible to defend people in this environment.
It's pissing into the wind, and the wind is people panicking about stuff they do not understand and have no real world context about.
In unrelated news, this is a good post about Mythos:
The dominant view in my filter bubble is that Mythos and other AI models will make exploit development, especially zero-days, dramatically easier, and that a vulnpocolypse is ahead of us. Easy enough… | Jeremiah Grossman | 20 comments
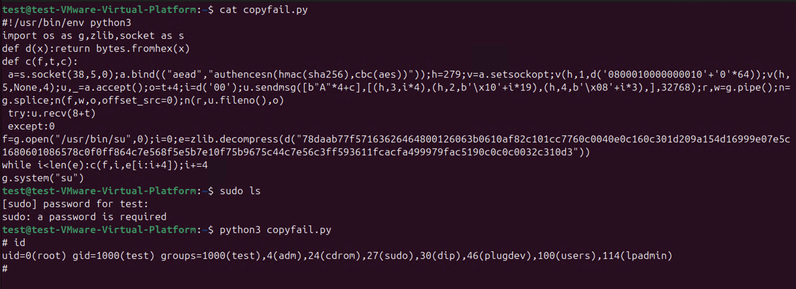
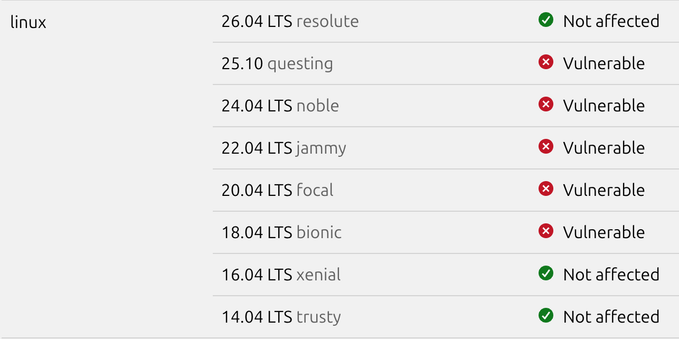
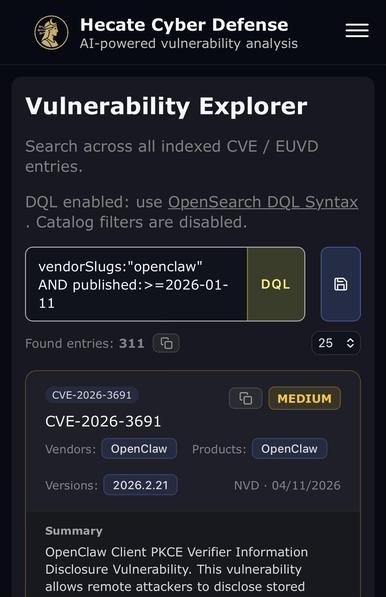
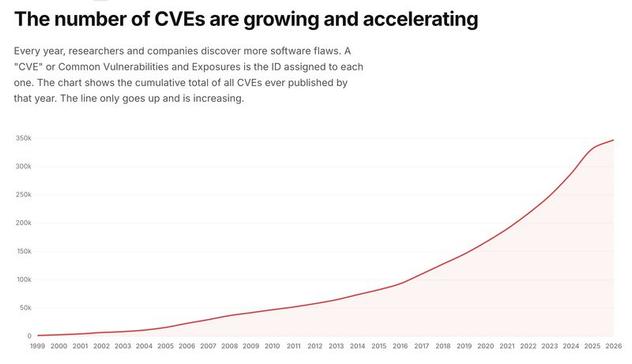
The dominant view in my filter bubble is that Mythos and other AI models will make exploit development, especially zero-days, dramatically easier, and that a vulnpocolypse is ahead of us. Easy enough that we should soon see an explosion in Known Exploited Vulnerabilities (KEVs). I’m watching the indicators closely, but in my view the hysteria is driving people towards protecting against what the adversary just doesn’t do, and just doesn’t care about. Cybersecurity will pay a price for bad advice. The fact is long before AI was generating code or finding bugs, we had years of rapidly accelerating CVE discovery and expanding exploit code availability. If vulnerability volume and exploit availability drove outcomes, KEVs would have scaled with it. The numbers don’t show that. For those unfamiliar with exploit development, most CVEs never get “weaponized” for in-the-wild campaigns, and for reasons beyond technical difficulty. Reachability: A large portion of vulnerable code isn’t externally exposed. It sits behind authentication, behind perimeter firewalls, or behind services that never face the Internet. If an adversary can’t reach it, it doesn’t matter that it exists. Reliability: A proof of concept proves something once. Real targets aren’t the lab. Versions differ, configurations drift, dependencies behave unpredictably. What works in one environment fails in another. Turning a bug into an exploit that works consistently across many targets is real work. That’s what adversaries need. Pervasiveness: Enough targets have to stay vulnerable long enough to matter. Many don’t. Vulnerabilities that are reachable, reliable, and pervasive often get patched, blocked, or otherwise neutralized before anyone builds a campaign around them. More capability doesn’t change what attackers need. It just makes it easier to produce things they still won’t use. The common mistake is to treat “might work,” or “works in the lab” as “will be used.” That leap is where a lot of the current confusion in cybersecurity starts. Want my advice. Protect your VPNs. Use MFA. | 20 comments on LinkedIn