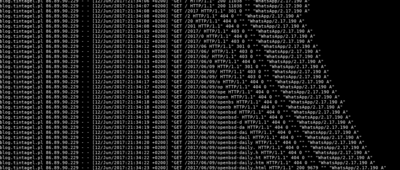
@WhatsApp @mulander and we have answers:
ad.1. yes, this happens in an encrypted chat
ad.2. yes, it's the user's device IP address (so that's a relief)
Consider, though: this means that an eavesdropper sitting on the same network can see the DNS queries and IP, and potentially the domain name and contents (if not an HTTPS site) of whatever a user is typing in an encrypted chat!
@rysiek @WhatsApp yeah, most people on birdsite think I'm mad at the fact they are requesting char-by-char due to bandwith.
It's an end 2 end encrypted communicator that does out of band GET requests leaking your IP, user agent + android version (with the image:og metadata), time at which you are writing the message and on top of that has a likely RCE vector with that content typ trick.