#ESETresearch discovered #GopherWhisper, a new China-aligned APT group that targeted a governmental entity in Mongolia. https://www.welivesecurity.com/en/eset-research/gopherwhisper-burrow-full-malware/
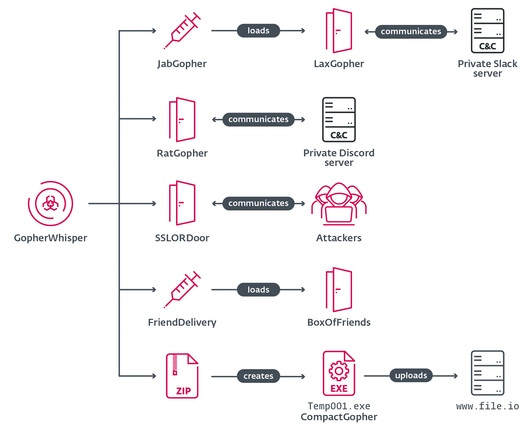
The group wields a wide array of tools mostly written in Go, using injectors and loaders to deploy and execute various backdoors in its arsenal.
Of the seven tools we discovered, four are backdoors – LaxGopher, RatGopher, and BoxOfFriends are written in Go, and SSLORDoor in C++. The rest comprise the injector JabGopher, the Go-based exfiltration tool CompactGopher, and the loader FriendDelivery.
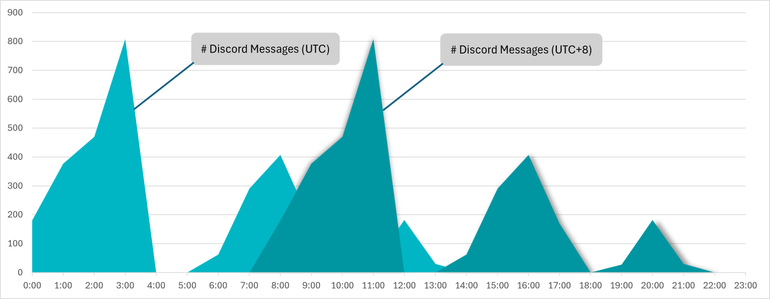
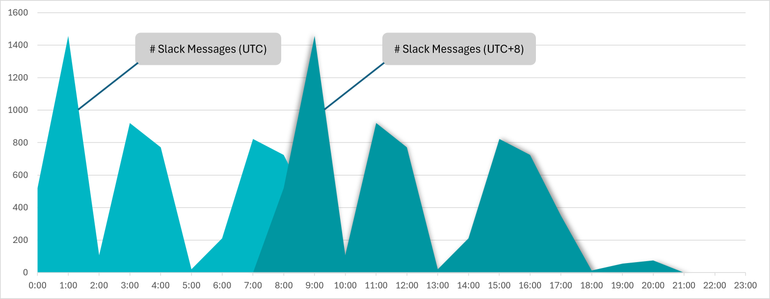
GopherWhisper abuses legitimate services, notably #Discord, #Outlook, #Slack, and file.io for C&C communication and exfiltration. We managed to extract thousands of Slack and Discord C&C messages, gaining insight into the inner workings of the group.
Timestamp inspection of the messages showed that the bulk were sent during working hours in the UTC+8 time zone, which aligns with China. We also discovered that the group’s Slack and Discord servers were being used as C&Cs for LaxGopher and RatGopher.
We presented these findings on April 15th, at the #Botconf2026 conference in a talk titled Meet GopherWhisper: Uncovering an APT’s secrets through its own words.
Our detailed analysis of GopherWhisper’s toolset and C&C traffic is also available in our latest white paper: https://web-assets.esetstatic.com/wls/en/papers/white-papers/gopherwhisper-burrow-full-malware.pdf IoCs can be found there, as well as in our GitHub repo: https://github.com/eset/malware-ioc/tree/master/gopherwhisper
The group wields a wide array of tools mostly written in Go, using injectors and loaders to deploy and execute various backdoors in its arsenal.
Of the seven tools we discovered, four are backdoors – LaxGopher, RatGopher, and BoxOfFriends are written in Go, and SSLORDoor in C++. The rest comprise the injector JabGopher, the Go-based exfiltration tool CompactGopher, and the loader FriendDelivery.
GopherWhisper abuses legitimate services, notably #Discord, #Outlook, #Slack, and file.io for C&C communication and exfiltration. We managed to extract thousands of Slack and Discord C&C messages, gaining insight into the inner workings of the group.
Timestamp inspection of the messages showed that the bulk were sent during working hours in the UTC+8 time zone, which aligns with China. We also discovered that the group’s Slack and Discord servers were being used as C&Cs for LaxGopher and RatGopher.
We presented these findings on April 15th, at the #Botconf2026 conference in a talk titled Meet GopherWhisper: Uncovering an APT’s secrets through its own words.
Our detailed analysis of GopherWhisper’s toolset and C&C traffic is also available in our latest white paper: https://web-assets.esetstatic.com/wls/en/papers/white-papers/gopherwhisper-burrow-full-malware.pdf IoCs can be found there, as well as in our GitHub repo: https://github.com/eset/malware-ioc/tree/master/gopherwhisper