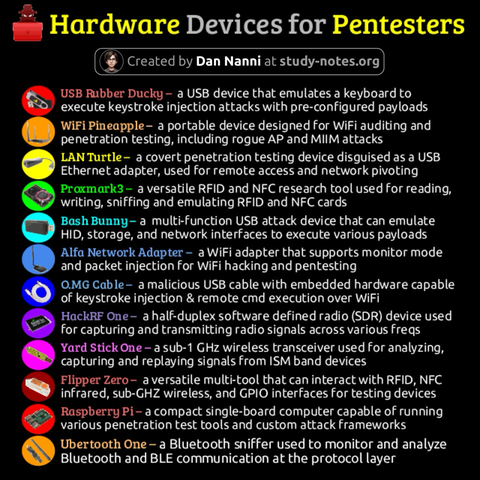
Red teamers don’t just rely on software. They carry purpose-built hardware—network adapters, SBCs, programmable USBs, and interception tools—to find and exploit real-world weaknesses.
Here are some portable devices commonly used in penetration testing😎👇
Find a high-res pdf ebook with all my cybersecurity related infographics from https://study-notes.org/cybersecurity-ebook.html