Looks like we have a live one here. Weird Rust maintainer phishing campaign using crates[.]ws:
https://discourse.ifin.network/t/bizarre-crates-io-phishing-campaign/232
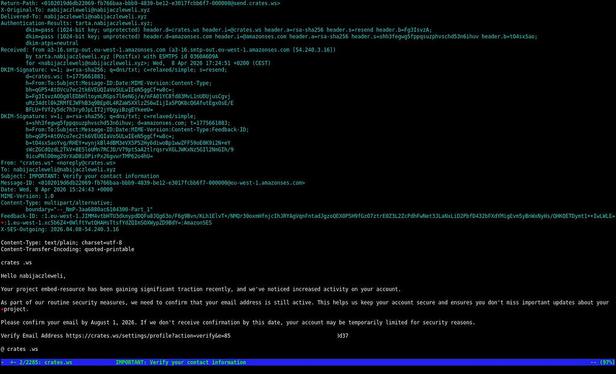
Bizarre crates.io phishing campaign
Observable: crates[.]ws Observable Type: Domain Details: Rust maintainer phishing email sending users to a bogus Crates website. Interestingly it looks like the .ws domain redirects to .io unless you provide it direct parameters. Unclear the intention though. Full URI in the email: https://crates[.]ws/settings/profile?action=verify&e=SOMENUMBER https://bsky.app/profile/nabijaczleweli.xyz/post/3miyodcruiuy2