Today's desktop computer challenge: For the case I need access to my home desktop from remote, I trigger boot through wake on LAN and then remotely unlock the encrypted hard disks through SSH.
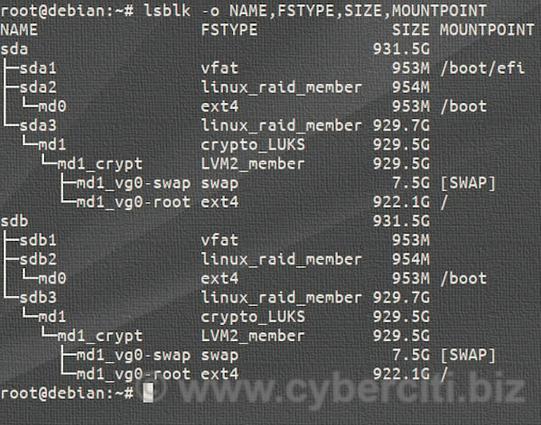
The challenge: Two encrypted hard disks. Solution: For the second hard drive add a key file located on the first hard disk as additional slot through cryptsetup, update the configuration in `/etc/crypttab`. Done.
1/n