Heads up FortiClient EMS users! CVE-2026-35616 (new) & CVE-2026-21643 - both unauthenticated RCE observed to be exploited in the wild! We fingerprint about 2000 instances globally, see public Dashboard: https://dashboard.shadowserver.org/statistics/iot-devices/time-series/?date_range=30&vendor=fortinet&model=forticlient+enterprise+management+server+%28ems%29&dataset=count&limit=100&group_by=geo&stacking=stacked&auto_update=on
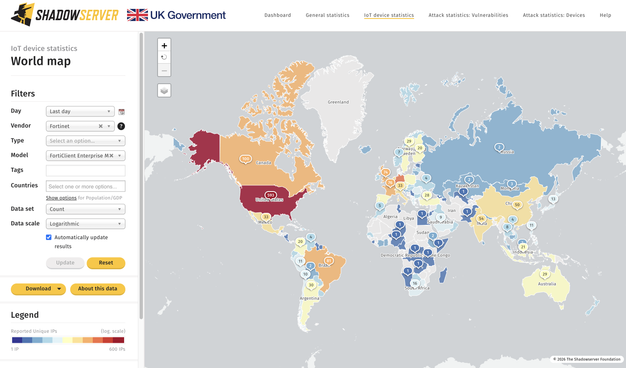
Top affected: US & Germany https://dashboard.shadowserver.org/statistics/iot-devices/map/?date_range=1&vendor=fortinet&model=forticlient+enterprise+management+server+%28ems%29&data_set=count&scale=log&auto_update=on
Raw IP data shared in our Device ID reporting https://www.shadowserver.org/what-we-do/network-reporting/device-identification-report/
If you receive data from us on exposed instances, check for compromise & patch!
Patch info:
CVE-2026-35616 (0day reported by Defused Cyber): https://fortiguard.fortinet.com/psirt/FG-IR-26-099
CVE-2026-21643: https://fortiguard.fortinet.com/psirt/FG-IR-25-1142