@jerry Attended a tech conference some years ago, and used a conference-specific email forwarder.
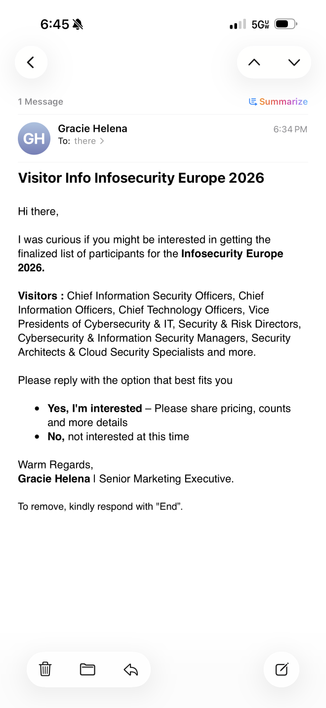
That email was used exclusively for the conference, and received only conference-related mail — until ~four years later, the newly-reorganized organizers and other senders all started spamming that email.
Old databases don’t go away.
But that email forwarder sure did.
yup. i've had "single use" emails that were dormant for over 12 years suddenly start spewing spam. i also regularly get spam to emails that have never existed (i've been only owner of the domain name) and never worked. a couple of these broken emails have been hit for decades.
old databases don't go away and are never cleaned up. just resold to other spammers.
in my case, it would just be postfix logs, a lot of which would just show sbl-xbl blocking of same. if that's useful, let me know.