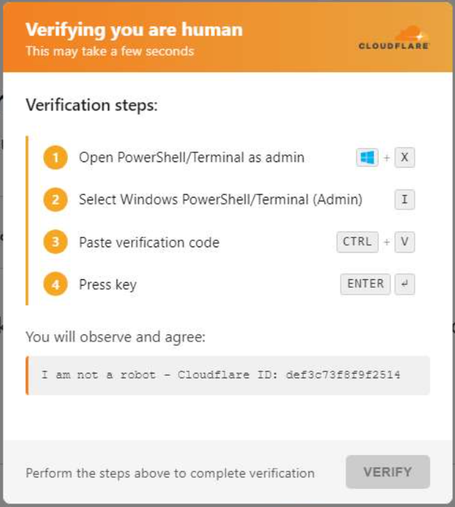
⚠️ #𝗦𝘁𝗲𝗮𝗹𝗖 𝗶𝘀 𝗻𝗼𝘄 𝗱𝗲𝗹𝗶𝘃𝗲𝗿𝗲𝗱 𝘃𝗶𝗮 𝗮 𝗖𝗹𝗼𝘂𝗱𝗳𝗹𝗮𝗿𝗲 𝗖𝗹𝗶𝗰𝗸𝗙𝗶𝘅 𝗳𝗹𝗼𝘄, masking malicious activity behind trusted services. Behavioral analysis exposed a PowerShell-based execution chain used to download and run the payload while attempting to evade detection.
👾 The Process Tree reveals the payload chain: powershell.exe ➡️ powershell.exe ➡️ y3gag2iu.3wq.exe (StealC 🚨)
Multi-stage PowerShell execution and hidden payload delivery make early confirmation harder, slowing triage. #ANYRUN Sandbox helps analysts quickly validate the attack and reduce investigation time.
👨💻 See the analysis session and collect #IOCs to speed up detection and response: https://app.any.run/tasks/48e6b68d-dfa2-423e-8e7c-24cf8a6ef85b/?utm_source=mastodon&utm_medium=post&utm_campaign=cloudflare_clickfix&utm_term=010426&utm_content=linktoservice
⚡️ Learn how #ANYRUN helps SOCs detect complex threats and contain incidents faster: https://any.run/features/?utm_source=mastodon&utm_medium=post&utm_campaign=cloudflare_clickfix&utm_term=010426&utm_content=linktosandboxlanding
⚙️ Technical details:
ClickFix flow on diddyparty[.]click triggers PowerShell via Win+X ➡️ I. A hidden command (-NoProfile -WindowStyle Hidden) enforces TLS 1.2, stages a random EXE in %TEMP%, pulls the payload via Invoke-WebRequest, executes it, and attempts cleanup. Full execution details are available in the Script Tracer tab.
🔍 IOCs:
diddyparty[.]click
3f0fe92c0e1c4663dcb851ce0fc97ddaed25b559be1d6e2cc0f66304ac652e38