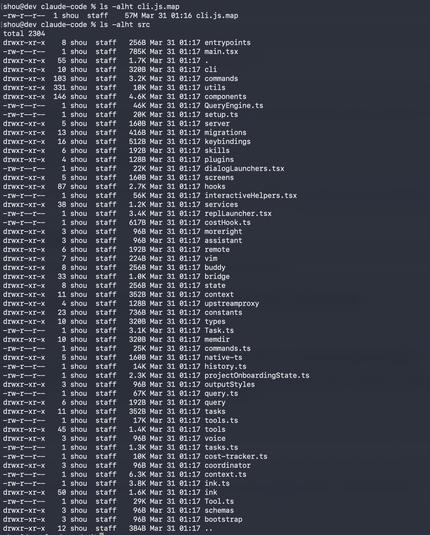
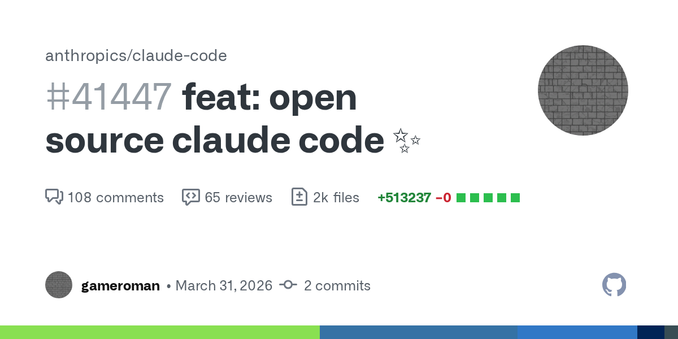
Two scenarios possibly resulting from today's Claude Code source code leak¹:
1. Attackers study the built-in permission system to figure out how to bypass it. Claude Code is the target here. It is strange that the software requesting permission is the same that enforces security boundaries, anyway.
2. Attackers distribute custom builds that
do nasty stuff like stealing API keys, running commands, backdooring code. Here, a specially crafted Claude Code is the attack vector.