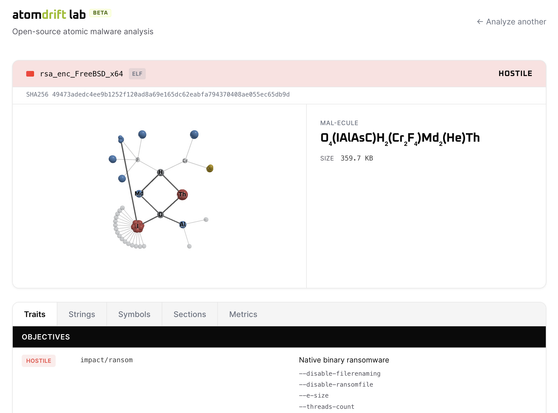
At the risk of spilling the beans too early... I grew tired of the constant barrage of supply-chain attacks afflicting the open-source community and decided to create a new open-source #malware scanner, named #Litmus.
This is part of a larger vision for intercepting supply-chain attacks, called The #Atomdrift Project. I want to empower everyone, from software marketplaces to teenagers at home, to catch the sorts of attacks we've recently seen against #Trivy and #OpenClaw.