how diffie hellman key exchange works
(with as little math as possible)
how diffie hellman key exchange works
(with as little math as possible)
(the above happened because i realized at some point that even though diffie hellman key exchange _uses_ things like "elliptic curves" or "modular arithmetic" to work, you do not need to actually _understand_ those things to understand the basic idea, and I thought that was cool!)
anyway this is what your computer is doing every time you make a HTTPS connection, to figure out what secret key to use to encrypt the connection
@b0rk That is a really nice explanation, thanks!
Your remark that “you do not need to actually _understand_ those things to understand the basic idea” reminds me of a math SE question I answered a while back: “My little cousin (12year) asked me about how emails are encrypted … Is there a teacher here who knows how to make her understand how to factor a number in to primes and what a prime number is?”
I had to answer twice. First I answered the question that was asked: I do know how to explain prime and composite to kids. But if what the the kid wants is to understand how emails are encrypted, the prime number thing is an unimportant implementation detail. I suggested explaining Vigenère ciphers instead.
Wow, thanks.
Excellent.
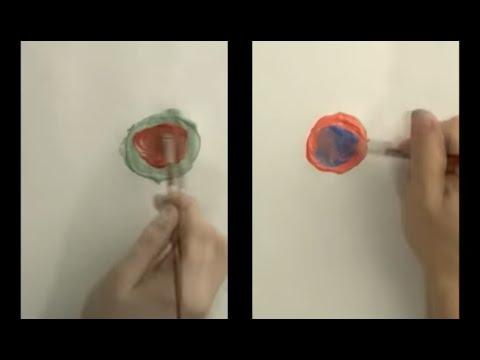
@b0rk @divVerent Not sure what you're asking but might it be like the mixing paint example in the video I linked to?
In that example, Alice and Bob share a common paint color to which they mix their secret color. They share that combination with each other, add their secret color again to arrive at a shared secret key. Horrible explanation on my part which the video does a much better job at.
But I probably am completely misunderstanding your question in which case ignore this!
@b0rk Great explanation. For anyone who may still not understand this or prefer a video, I highly recommend watching this one:
RE: https://infosec.exchange/@sophieschmieg/116246805758237078
@b0rk you don't just get Diffie to sign it?
@pmb00cs one interesting way the mixing paint metaphor doesn't work (imo) is that when you're mixing paint the two colours you're mixing both have the same "type", and it's a symmetric operation (a mixed with b is the same as b mixed with a)
but in diffie hellman the operation is not symmetric at all, like the type of the function is more like f(type1, type2) => type1
I think saying that "s" and "a" are both "numbers" might be a bit of an oversimplification in that sense
@pmb00cs but I definitely have a tendency to be overly critical about the specifics of metaphors in a way that's not necessarily helpful :)
the paint thing is cool!
@b0rk I mean, there's a point where a metaphor doesn't work anymore, because it's not the truth, just a way to explain part of the truth. If you need perfect accuracy you're just explaining reality.
The paint metaphor also breaks down because there are tools for recreating paint colours accurately from pure pigments. Do that for (sxa), (sxb), and s, and you recover a and b. So it's not really suitable as a form of key exchange. But it is easy to understand on a basic level.
@b0rk you can do it without maths at all. Say I want to give you my bicycle, but our schedules just will never work out for me to give you it directly. Well, we pick a place both of us can access, say outside the train station. I lock my bike up at a designated spot and go about my day. You come along with your own lock and use it to fasten the bike to the same spot without interfering with my lock, then go about your day. At some point I remove my lock, after which you can remove yours and gain a bicycle.
As I understand it, such a protocol was the inspiration for DH key exchange. Picking a spot is picking a generator. Locking is exponentiating. Locks not interfering is the commutativity property.
It's the explanation I always use when TAing cryptography

@SnoopJ what do you mean by mixed up punctuation?
it’s trying to explain how on an elliptic curve, you start with an initial point s on the elliptic curve, choose a random integer x , and then add that point s to itself x times (using elliptic curve addition) to get the result of the “magic function”