Seeing FQDNs like "mtmoqiuq.20.218.142.124.static.hostiran[.]name" and "sgrwnbid.172-202-98-170.cloud-xip[.]com", we first thought some ASNs could be exploited similarly to the ".ARPA abuse" we described in one of our recent blogs. Turns out we were overthinking it... This kind of "DNS abuse" is so straight forward... We're not sure it qualifies as DNS abuse...
Here is what is going on: Whatever IP address you prepend to "static.hostiran[.]name" creates a hostname which resolves to this IP... That is it! Same goes for cloud-xip[.]com!
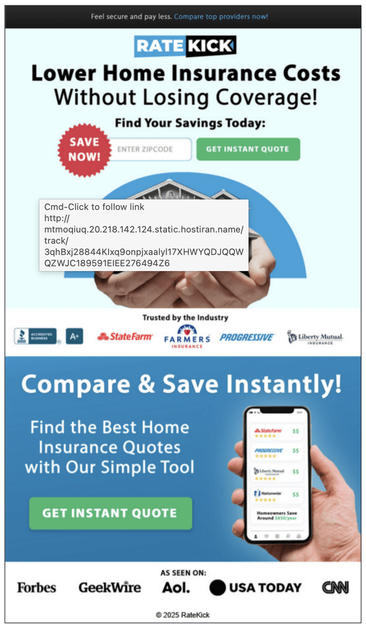
We've seen these kinds of hostnames a lot in SPAM emails recently, like the one we screenshot below which loads an image from a CDN as a giant hyperlink. We aren't sure why malicious SPAM actors bother to use this trick in their email links... If they control an IP, they can use it directly in URLs. They don't need a domain name!? And it isn't like this bypasses a firewall... If their IP is blocked, queries to those FQDNs will be too...
Our best guesses are that:
- Using hostnames rather than IPs helps them bypass SPAM email detection?
- And / or it enables them to create "subdomains", which they seem to be doing to track something, either SPAM campaigns, or their victims.
Technically, this could be used to create lookalike FQDNs. Those examples look like random subdomains, but literally anything can be prepended to the IP, so the only limit is your imagination! Not the most convincing lookalike by any means... but we've seen worse!
Here is an example of how this can be abused to both, load content from literally any IP, and create low quality lookalikes:
https://urlscan.io/result/019d1b3d-b94e-70f9-aae7-ecf5a02e3c89/
#dns #threatintel #threatintelligence #cybercrime #cybersecurity #infosec #infoblox #infobloxthreatintel #spam #scam