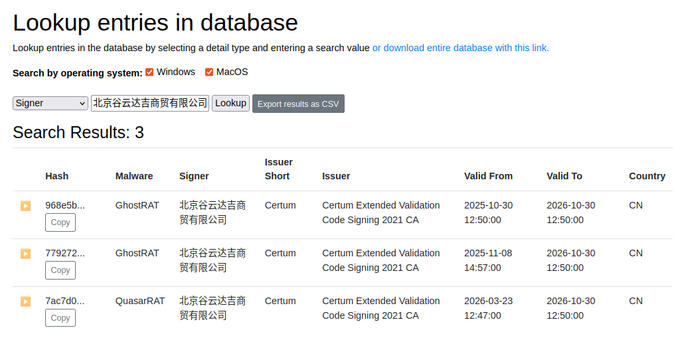
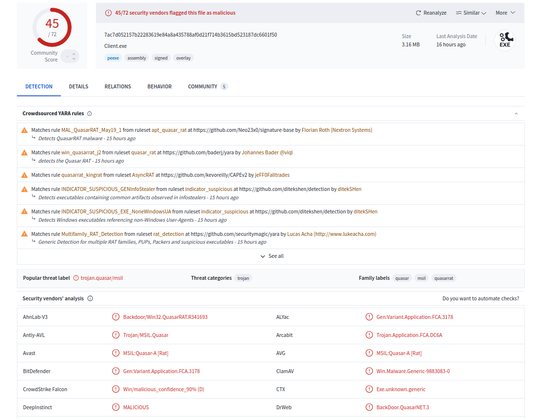
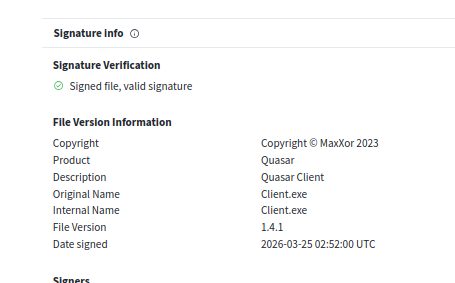
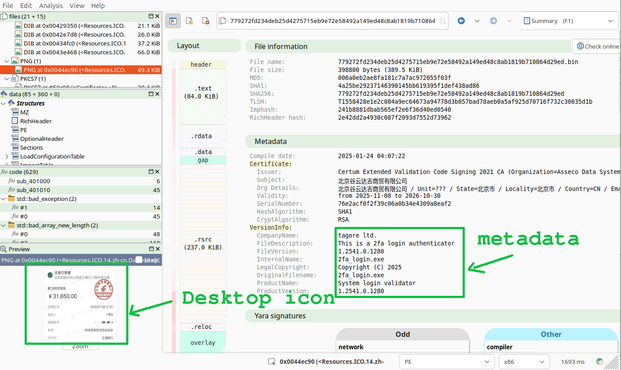
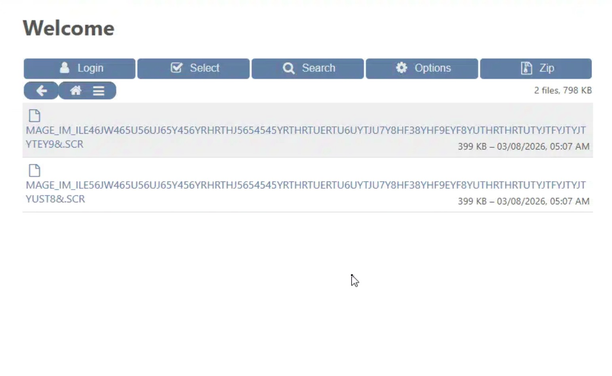
QuasarRAT signed by "北京谷云达吉商贸有限公司"
This signer previously signed GhostRAT.
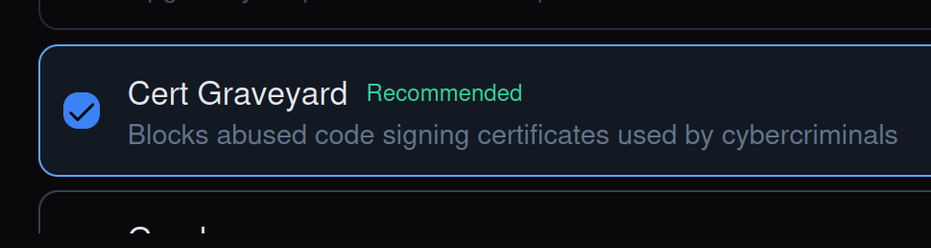
Cert was revoked.
They received new certificate.
Revoked.
New certificate.
Revoked.
If I didn't have a database with records, I'd think I was insane.
h/t @malwrhunterteam
1/6