Poisonseed has successfully phished enterprise email accounts for over a year to further their crypto seed phrase poisoning attacks. 🎣 ✉️ 💸
It's been one year since @troyhunt's Mailchimp phishing incident (https://www.troyhunt.com/a-sneaky-phish-just-grabbed-my-mailchimp-mailing-list/) which resulted in threat actors downloading his entire email list and creating an API key likely in an attempt to send mass emails from his account.
Before we get into some fresh domains you can hunt, here's a bit of background on this ongoing threat...
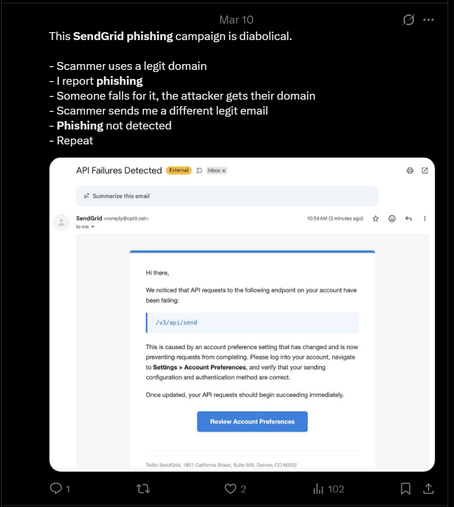
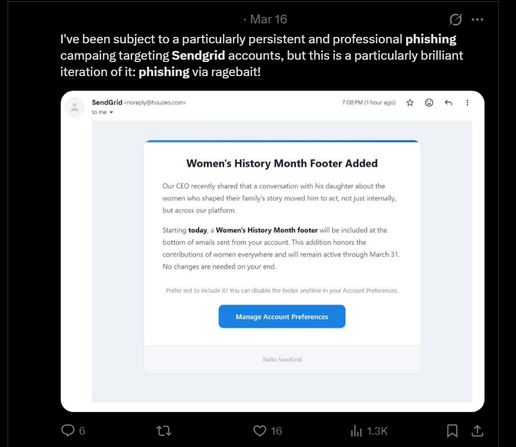
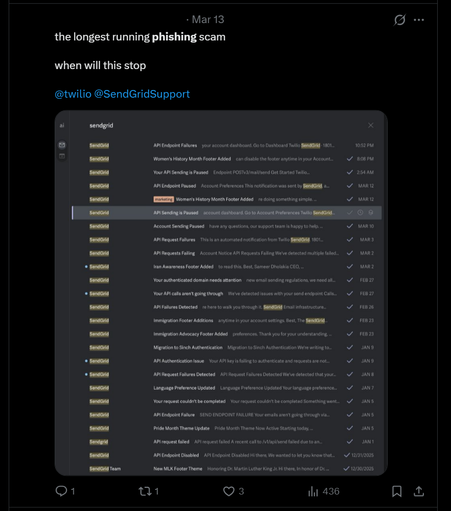
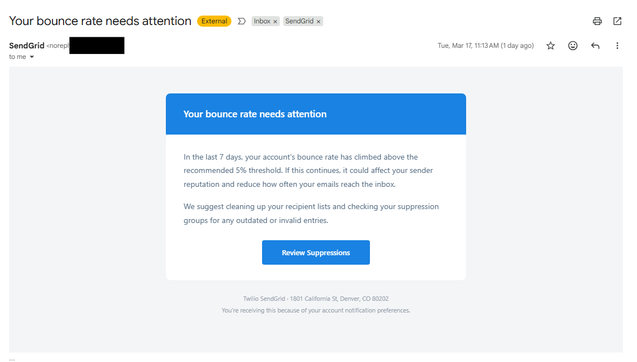
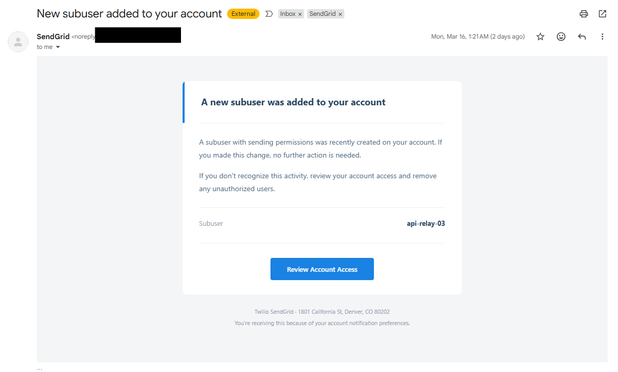
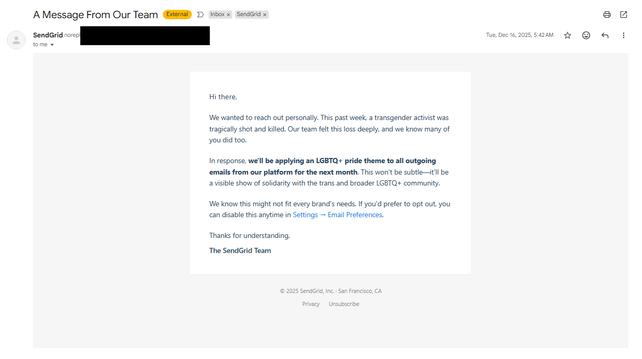
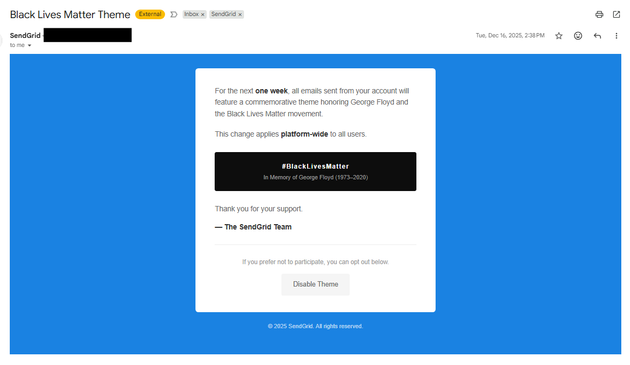
The threat actors behind this campaign are seemingly associated with The Com / Scattered Spider threat actors and use a compromised email account to send CRM phishing emails and also crypto seed phrase poisoning / crypto phishing emails. They essentially compromise a CRM to send more CRM phishing emails from it – a supply chain compromise that just keeps spreading -- very clever! The threat actors are targeting Mailchimp, Sendgrid, ActiveCampaign and allegedly other CRM providers.
We've had some great writeups in the last year on this threat including:
Validin: "Pulling the Threads on the Phish of Troy Hunt" @ https://www.validin.com/blog/pulling_threads_on_phishing_campaign
Silent Push: "PoisonSeed Campaign Targets CRM and Bulk Email Providers in Supply Chain Spam Operation" https://www.silentpush.com/blog/poisonseed/
NViso: "Shedding Light on PoisonSeed’s Phishing Kit" https://blog.nviso.eu/2025/08/12/shedding-light-on-poisonseeds-phishing-kit/
Domain Tools: "Newly Identified Domains Likely Linked to Continued Activity from PoisonSeed E-Crime Actor" https://dti.domaintools.com/research/newly-identified-domains-likely-linked-to-continued-activity-from-poisonseed-e-crime-actor
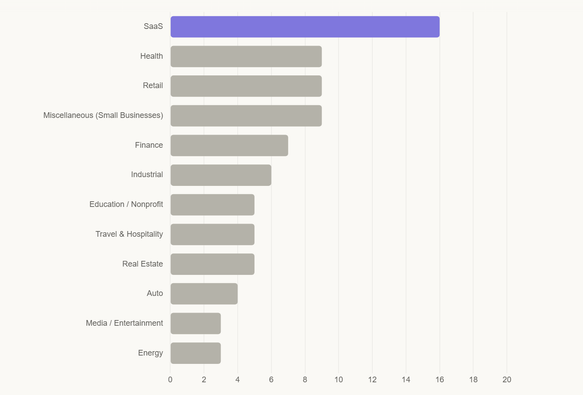
Over the last year, Poisonseed have successfully phished *dozens* of major organizations, seemingly with no or minimal public disclosures about these incidents from impacted organizations. And while we don't share victim details, we have a breakdown of the industries who have been impacted by the CRM phishing campaigns (essentially every major industry):