Handala claim to have hacked and wiped 74 servers at AGAS - https://www.agas.co.il - an Israeli MSP, MSSP and cloud reseller.
I’m not sure the size of the org stacks up with Handala’s claim. Also, 74 servers is not a lot.
I’ve reached out to AGAS to see if they want to comment.
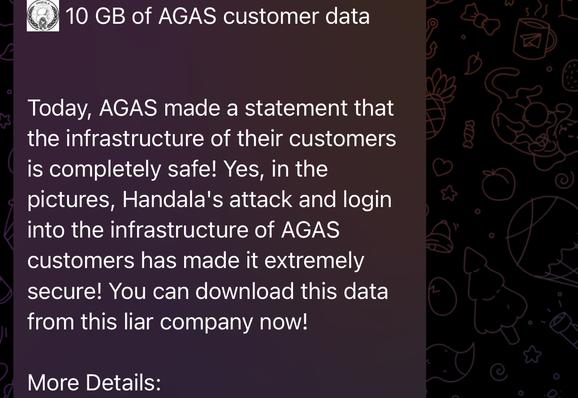
Handala claim to have released 10gb of customer data for AGAS.
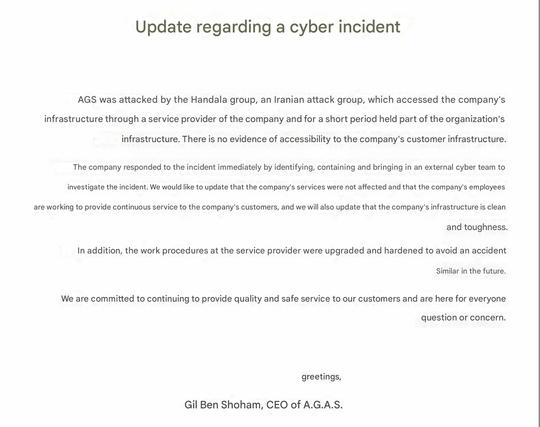
It does appear AGAS has a security incident going on. AGAS declined to comment when asked.
Handala say have hacked and dumped IM Cannabis aka IMC - https://imcannabis.com/ - using their access via AGAS, their MSP.
They also implicate another company, NDN Security - https://www.ndn-security.com/
Handala claims to have done a leak and wipe of Elad municipality.
Elad's website is offline, and there's an Israeli media report of some kind of cyber incident.
Handala typically over exaggerate data volumes exfiltrated.
Handala have posted photos and internal diagrams of, they claim, Shimon Peres Negev Nuclear Research Center.
The data appears to have come from Soreq. I have confirmed Soreq was owned, via the IAEA.
A few things have happened with Handala over the past few days which I haven’t covered - they’ve been dumping cloud backup photos and making threats, including about family members. I didn’t want to cover it.
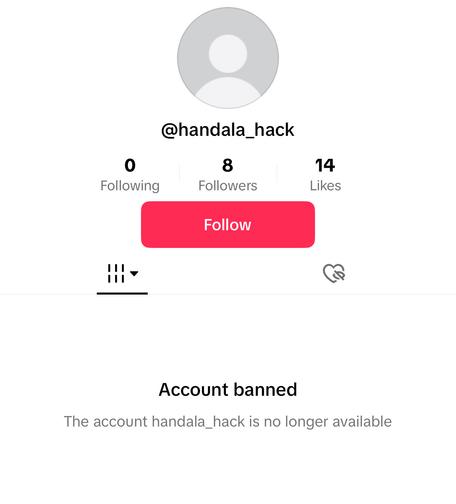
All but one of the Handala Telegram channels has been shut down tonight.
Handala continues to be crazy town, with data dumps of what is allegedly to be SSV Network, a blockchain company.
Handala claim they can link it (SSV Network) to Unit 8200, the Israeli intelligence agency. So far this appears to be without proof.
I’m going to guess, based on this post, they plan to post more tomorrow about Unit 8200.
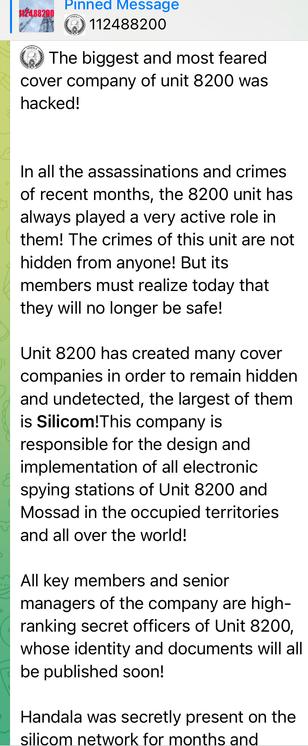
So with the Unit 8200 stuff and Handala, their latest claim is they gained access to Silicom Limited (an IT services and networking company) and exfiltrated data, and that Silicom is a front company for Unit 8200.
Presented evidence includes a video accessing an internal VMware vCentre cluster with about 50tb of storage.
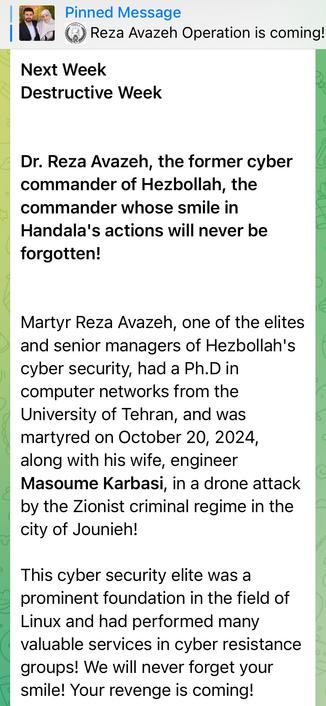
Masoumeh Karbasi & Reza Avazeh were killed in a drone strike in Lebanon in October. As far as I can see nobody knew why publicly, Handala’s linking Reza to Hezbollah and their cybersecurity appears to be a first.
His children were invited to meet ‘Supreme Leader of the Islamic Revolution’ that week. https://farsi.khamenei.ir/news-content?id=58050
Handala say they plan their most destructive hack so far this weekend, over the fate of Reza Avazeh
There’s even a video, but sadly no hoodie wearing hackers
Handala claim to have gained access to
CaaB Cloud (https://caab.cloud), aka Cloud as a Business, posting a video of administrator access. CAAB Cloud describe themselves as “The MSP’s Cloud” in marketing.
CAAB Cloud is owned and operated by GNS in Israel, aka https://gns.cloud
It is unclear if the claims are credible. CaaB’s status page suggest a ~10% availability impact in one of their Israeli datacenters three days ago on cloud VM. https://status.caab.cloud
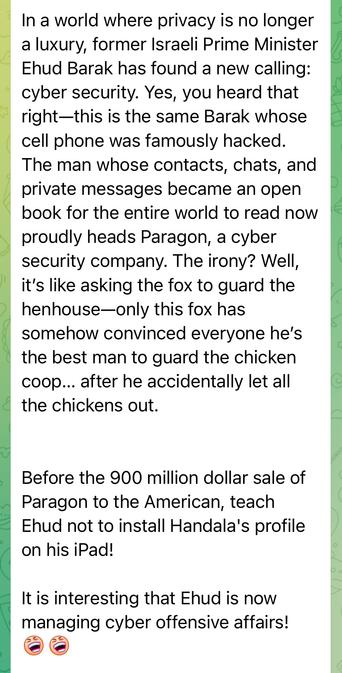
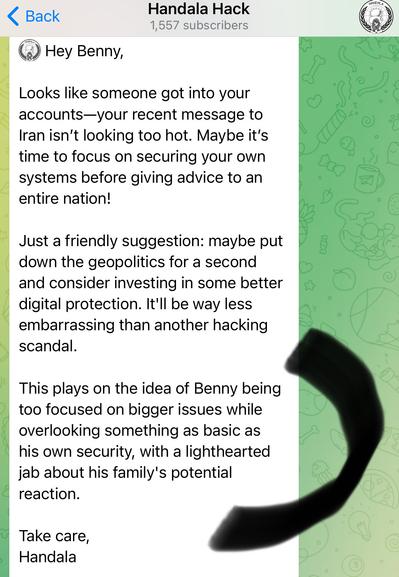
I wrote up the Handala attack on ReutOne, includes the first IoCs on Handala's python trojan
https://doublepulsar.com/handala-attempts-a-supply-chain-hack-via-reutone-001aa3cc684f
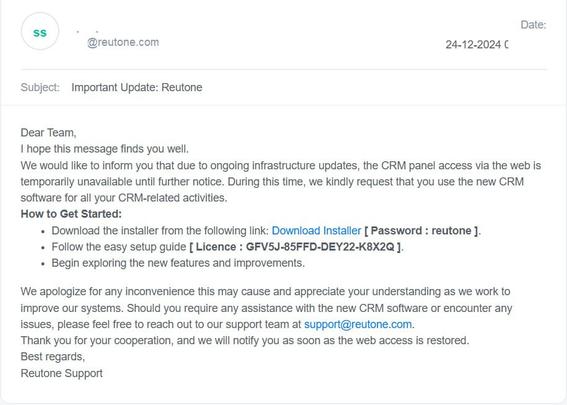
Handala has also defaced ReutOne’s website, and published videos of RDP access to ReutOne’s internal network, eg Active Directory Certificate Authority etc. https://web.archive.org/web/20241226141650/https://www.reutone.com/
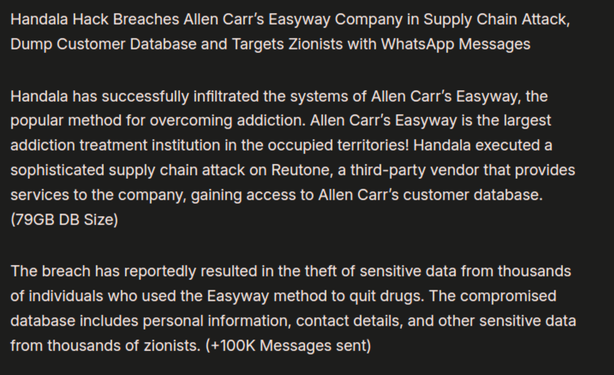
Handala claim they hacked Allen Carr's Easyway via ReutOne.
Two points:
a) I legit thought they had hacked UK national treasure Alan Carr for a moment
2) "reportedly", lol. ChatGPT doing overtime for Handala.
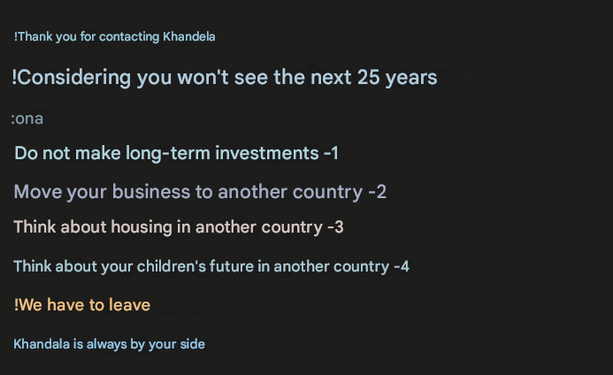
The '100K messages sent' thing is a reference to Handala abusing WhatsApp Business accounts, my English translation of message they've been sending.
Handala claim they will be wiping Mossad’s financial network today. Also, they appear to have purchased ChatGPT premium.
One note, they fully respected the dates of the ceasefire last time but apparently aren’t bothered this time? #handala #threatintel
Edit: derp, it was Cyber Toufan who respected the ceasefire, not Handala.
Handala claim to have done a hack and wipe of Zuk Group, an Israel group of financial companies. Their website has been defaced as of writing.
Handala posted a series of videos appearing to show access to their internal network.
Handala also claim the company is a front for Mossad. They offer no evidence of that bit.
Handala got booted off Telegram after the Zuk Group hack.
They’re back on another channel and posted:
“وَ كَمْ قَصَمْنا مِنْ قَرْيَةٍ كانَتْ ظالِمَةً ... بَلْ نَقْذِفُ بِالْحَقِّ عَلَى الْباطِلِ فَيَدْمَغُهُ فَإِذا هُوَ زاهِقٌ ...”
Which translates to
“How many a city have We destroyed which was unjust... Rather, We cast the truth upon falsehood, and it destroys it, and at once it departs...”
Handala claim to have hacked the Ministry of National Security in Israel, activated red alert to get people into shelters, closed the doors, then played a song and wiped the system.
Very unclear how widespread or credible this is, although some Israeli social media posts show devices going off and playing songs.
There’s some coverage in Israeli media suggesting a focus on schools, with Israeli authorities acknowledging the incidents.
https://www.mivzaklive.co.il/archives/879473
https://www.inn.co.il/news/659713
For the record Handala claims they sent 5million text messages at 8am this morning, UK time.
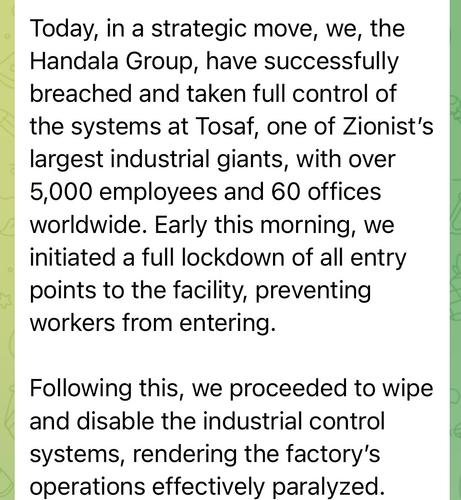
Handala claim to have done a hack and wipe of Tosaf, a plastics manufacturer.
Screenshots show apparent Windows domain admin access, and they attach CCTV videos of themselves playing songs into a factory and an office, with workers looking confused.
Handala have been fully kicked off Telegram, including their backup channel.
Achievement unlocked as I can't remember a group ever getting fully booted.
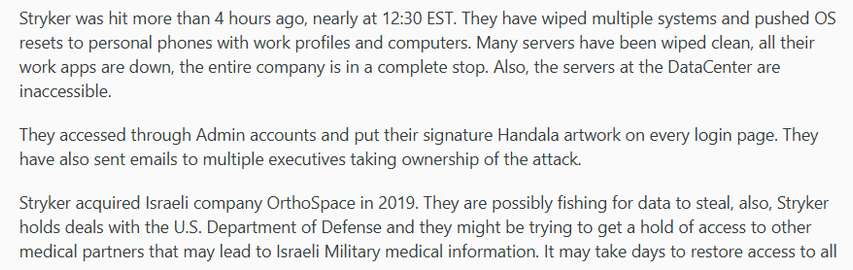
Handala appear to have fully wiped a company called Stryker, a global healthcare company.
Not in the link but they've got into AD, and wiped all the devices with Intune etc etc.
https://www.irishmirror.ie/news/irish-news/stryker-cyber-attack-thousands-irish-36850017
There’s an entire thread tracking Handala above btw, goes back multiple years. Some bits need follow links to the thread as I broke it.
Their MO is break in, lay low for months, when target interesting exfiltrate data and then delete everything including org backups. They pivot to domain admin early and then sit on access for later. They live off land and live off org IT documentation.
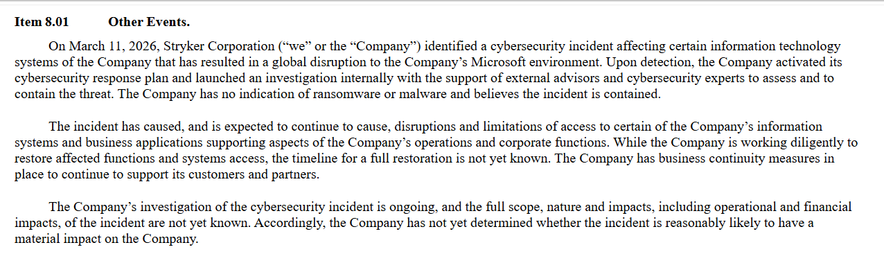
Stryker have filed an 8-K with the SEC for their wiper incident.
"The Company has no indication of ransomware or malware and believes the incident is contained."
Almost like Handala lived off the land..
https://www.sec.gov/Archives/edgar/data/310764/000119312526102460/d76279d8k.htm
Stryker have a liveblog of their security incident, linked from the front page of their website:
https://www.stryker.com/gb/en/about/news/a-message-to-our-customers-03-2026.html
tl;dr is most customer systems aren't impacted as they run on Linux, but their corporate Windows systems are toast so please hold the line.