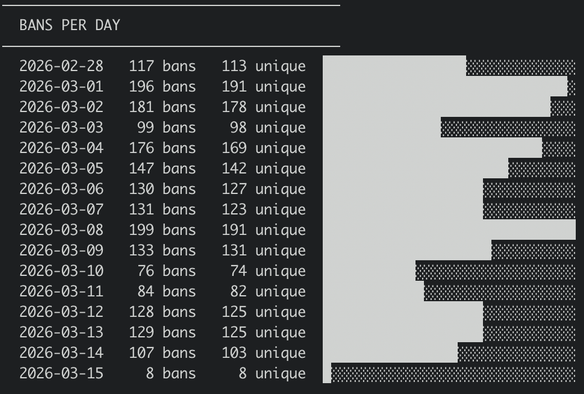
I have a persistent little botnet that has been hammering my non-standard ssh-port on my personal VPS for a while since it found it some weeks ago. For a long time I just ignored it, but today I decided to fight back a little.
First, I had claude write me a little script to fetch abuseipdb and turn it into a ipset rule to block everything before it even hits the server. But turns out the free level of abuseipdb only includes the top 10k ones. So I included a otx one also, but still did not catch all of them. Now I added blocklist.de which had the last ones. Let's see where that takes us.
Why am I doing this you might wonder? Is getting your ssh brute forced not part of life on the internet?
Probably, but I like making life hard for attackers even if it's mostly symbolic. First I had a ssh-tarpit with the hopes that it would tie up the scanners, but I think most scanners nowadays written in vibed in golang and it handles concurrency without trouble.
So next I thought I'd impose some cost on their botnet, by reporting them to abuseipdb. If that "burns" their IP and forces them to find a new one, then it's a win. But I was still getting too many connections that was already on the list, so me saying +1 it's bad was not adding much value.
So I thought, what if I block "all" the "known" ones. That means that if someone gets through and reported to abuseipdb, maybe that was a clean address that is now marked bad and might not work against others.
I guess it's like trying to put out a forest fire with a bucket of water, but it's at least something. And at least it cuts down on the noise on my server 10x.