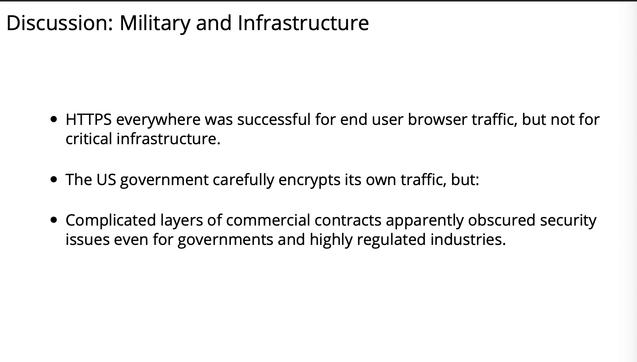
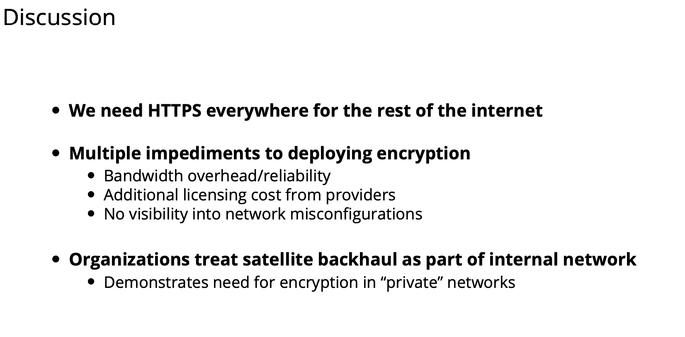
telecom just broadcasting in the clear
#realworldcrypto
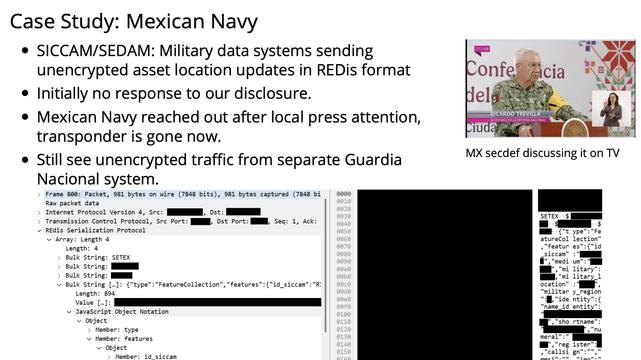
"It's really hard to disclose vulns to foreign militaries"
#realworldcrypto
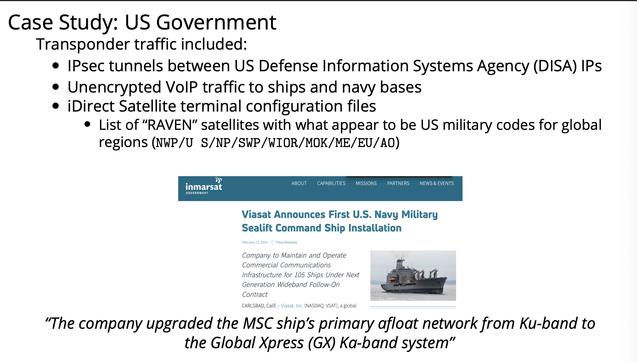
US gov, when we finally got in contact, took config mistakes very seriously
#realworldcrypto
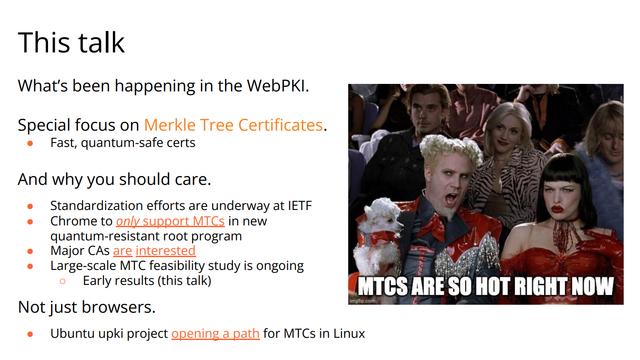
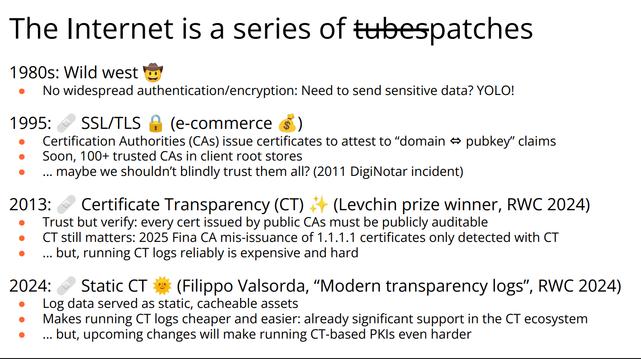
Next up, '(Dis)patches from the Web PKI: Fina, Static CT, MTC, and PLANTS', presented by Luke Valenta
#realworldcrypto
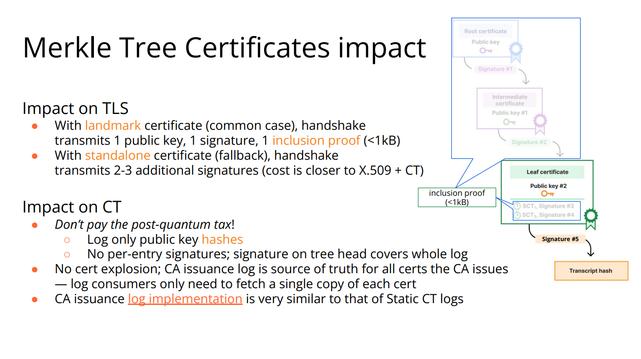
Merkle Tree Certs!
#realworldcrypto
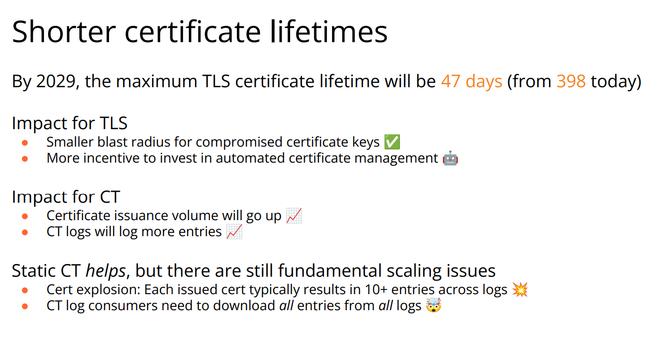
Shorter cert lifetimes
#realworldcrypto
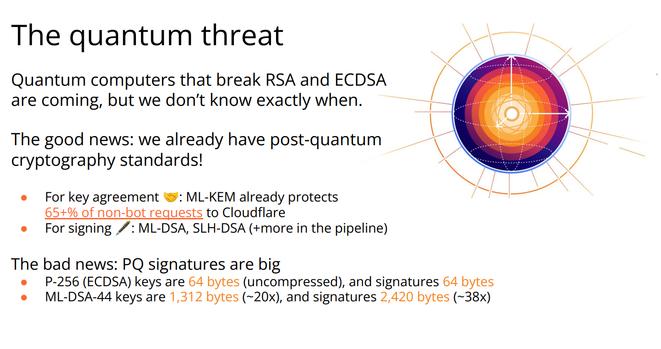
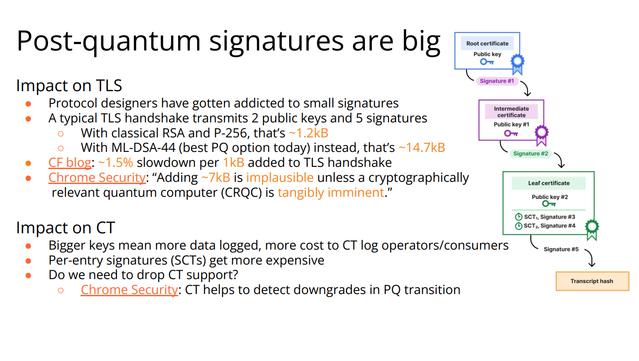
PQ sigs are beeg
#realworldcrypto
In TLS in browsers will add ~7KB to each handshake, ~10% slowdown
#realworldcrypto
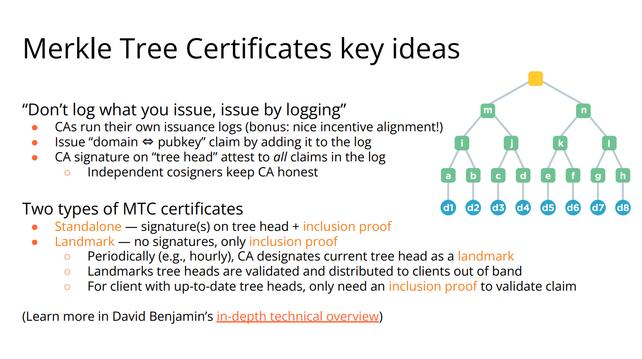
Instead of achieving transparency by logging what is issued, we issue by logging and get both at once
#realworldcrypto
Smaller even when using PQ sigs, no cert explosion
#realworldcrypto
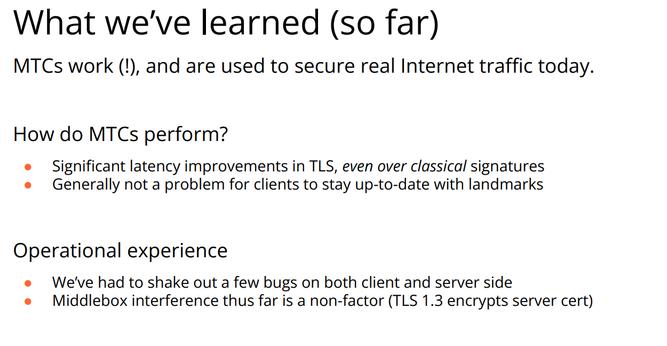
'landmark' MTCs, faster than classical?
#realworldcrypto
Join PLANTS!
datatracker.ietf.org/wg/plants/
#realworldcrypto
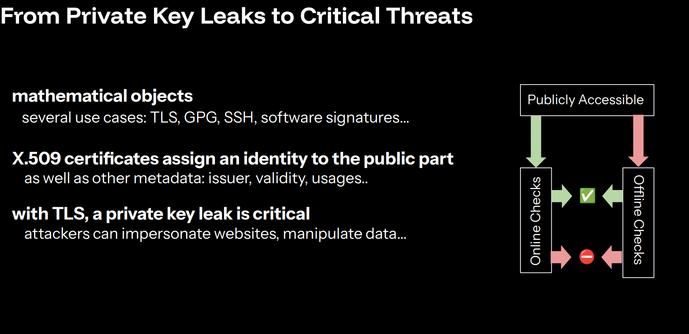
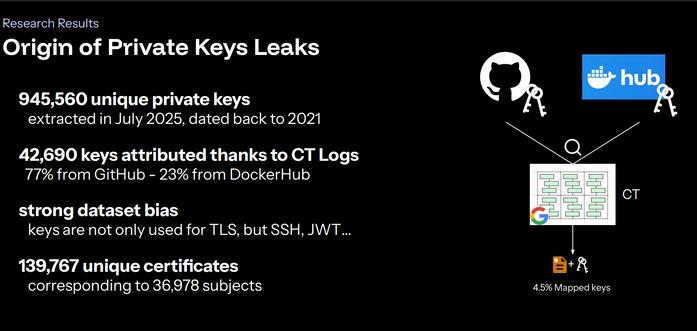
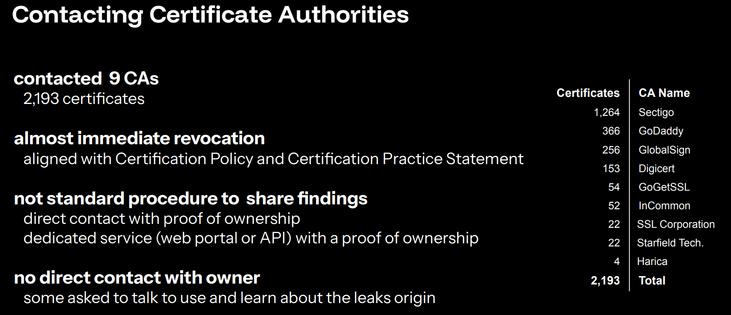
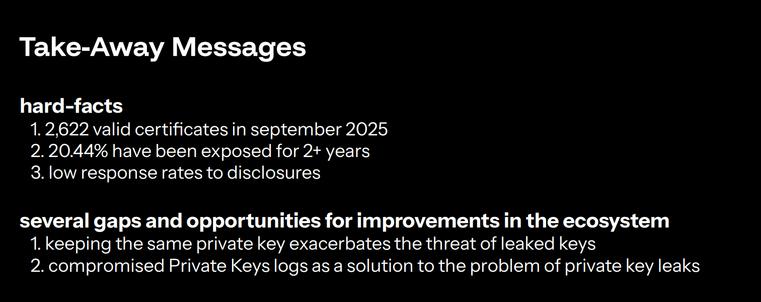
Next up, 'Private Key Leaks in the Wild: Insights from Certificate Transparency', presented by Guillaume Valadon and Gaëtan Ferry
#realworldcrypto
Leaking private keys
#realworldcrypto
Cert revocation is rarely used
#realworldcrypto
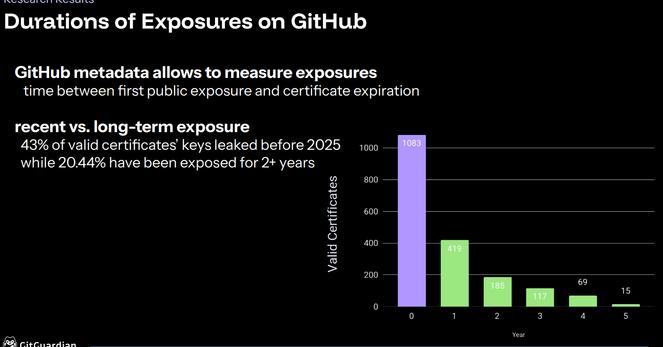
measuring exposure duration
#realworldcrypto
yeesh
#realworldcrypto
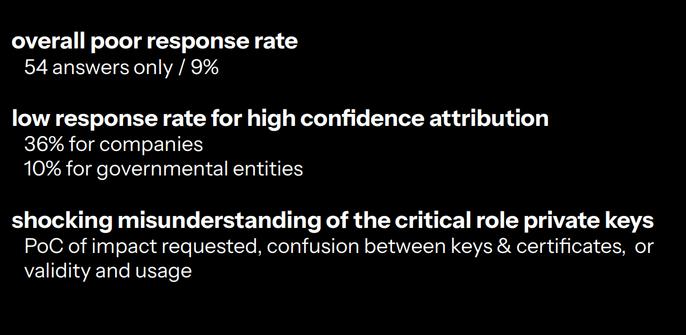
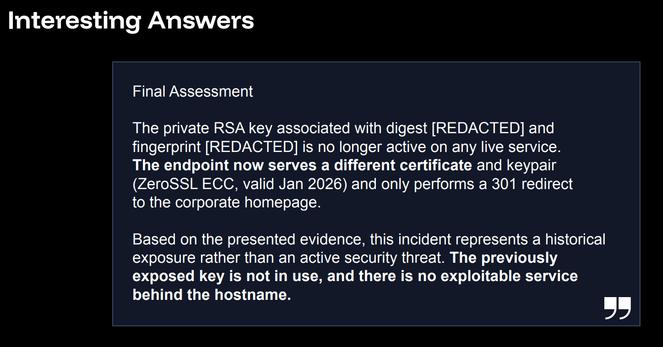
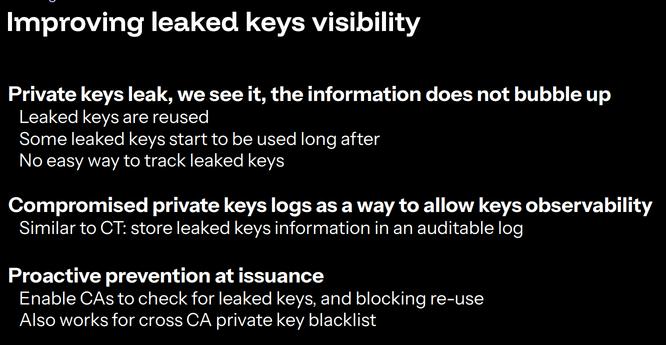
Public log of leaked private keys?
#realworldcrypto
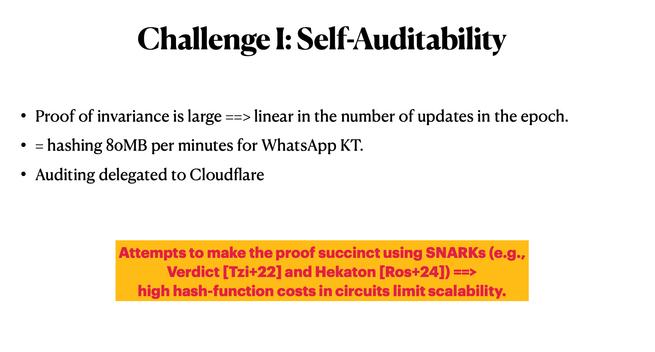
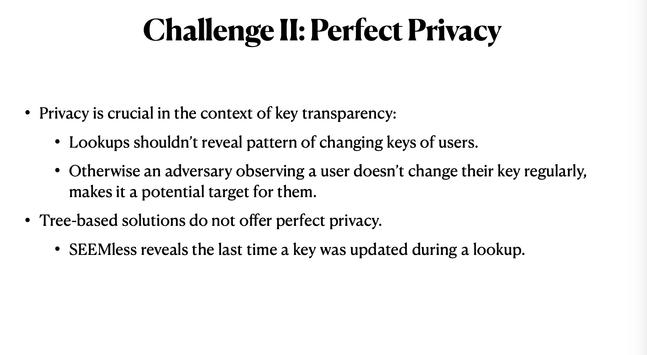
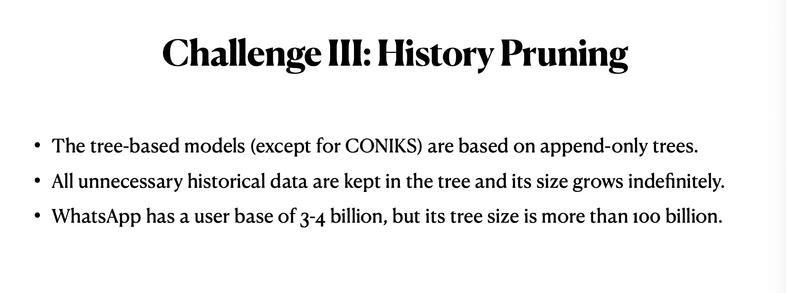
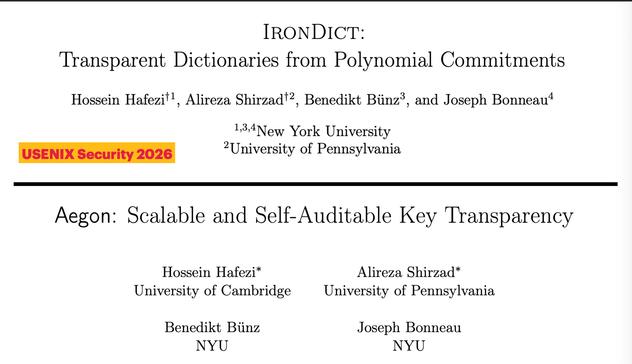
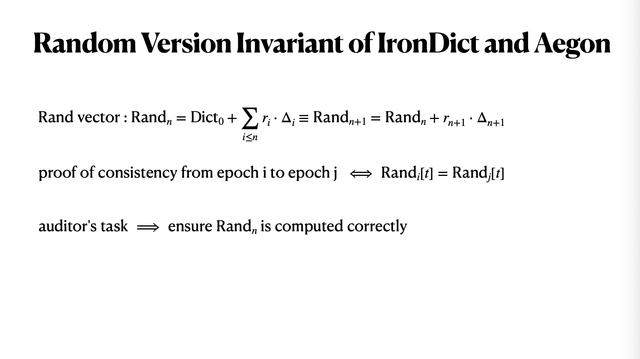
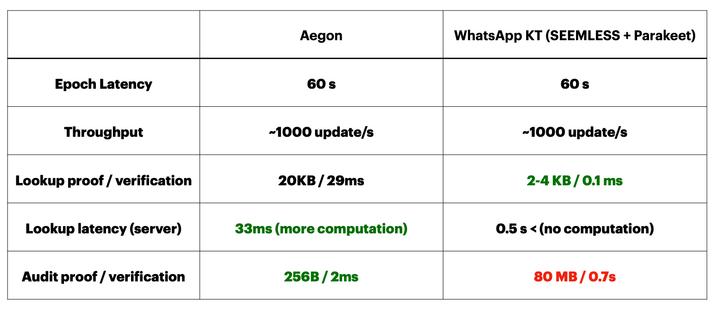
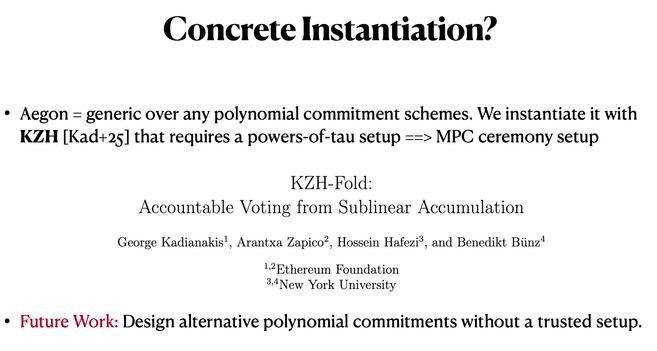
Next up, 'Self-Auditable Key Transparency at Scale', by Hossein Hafezi
#realworldcrypto
Nice
#realworldcrypto
Oop, trusted setup
ia.cr/2025/1580
#realworldcrypto
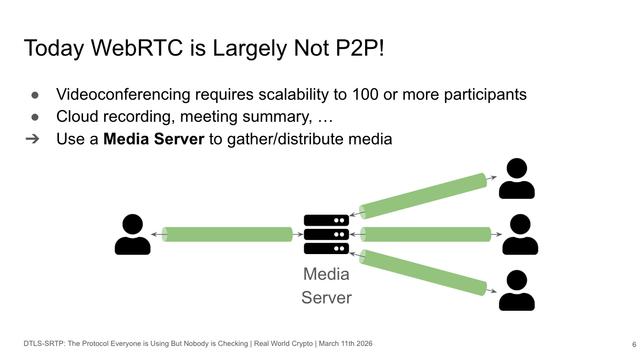
Next up, 'DTLS-SRTP: The Protocol Everyone is Using But Nobody is Checking', presented by Robert Merget
#realworldcrypto
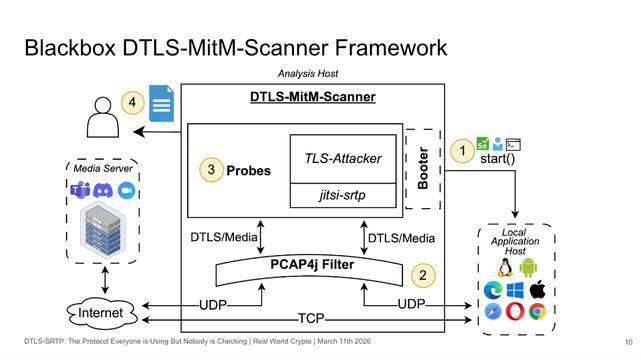
Let's build a scanner!
#realworldcrypto
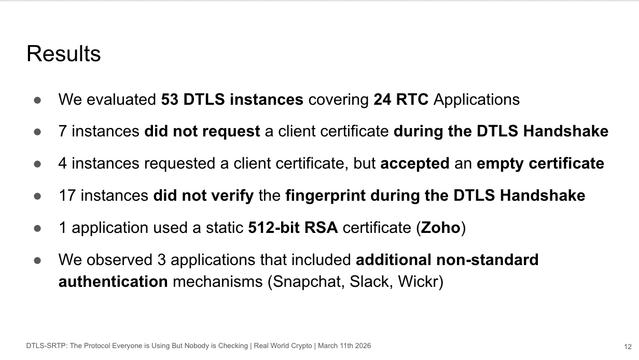
Found 53 DTLS instances
#realworldcrypto
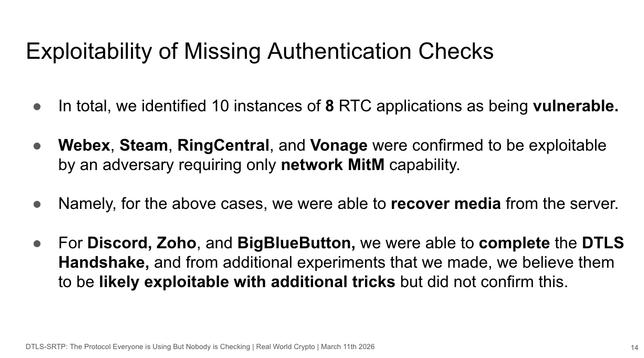
Missing auth checks, vulnerable to network man in the middle, including Webex
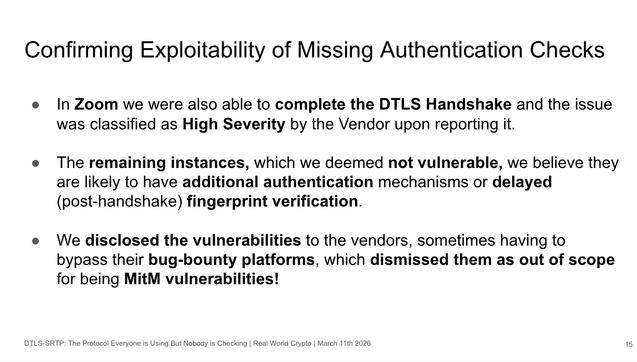
#realworldcrypto
Sev: high bug in Zoom
#realworldcrypto
Q: Did you look at E2EE real time communication that used sframe as well?
A: MIght've been Zoom, didn't observe any other cases
#realworldcrypto
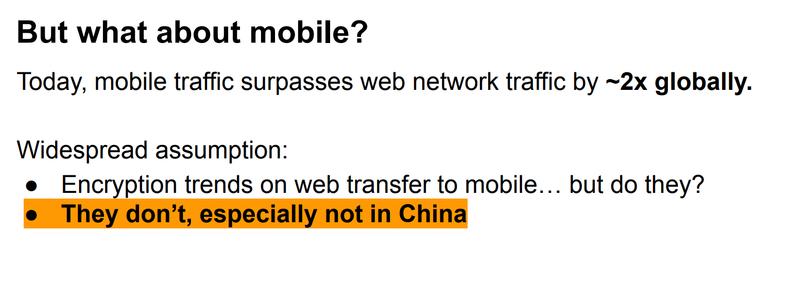
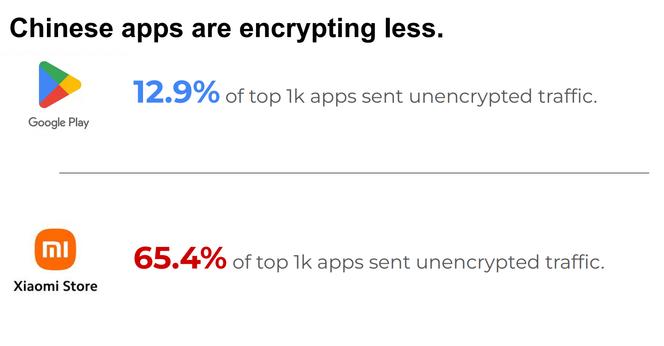
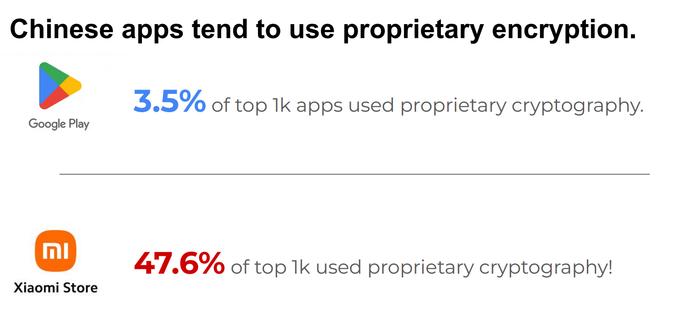
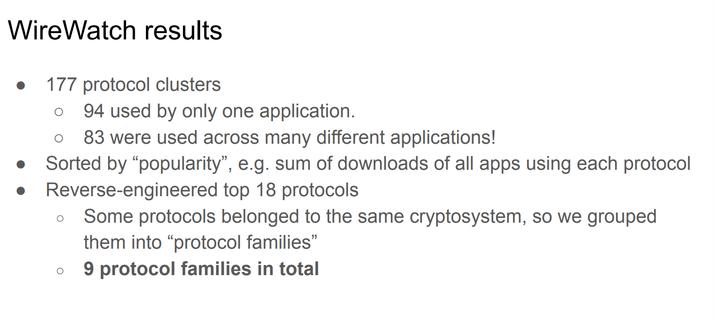
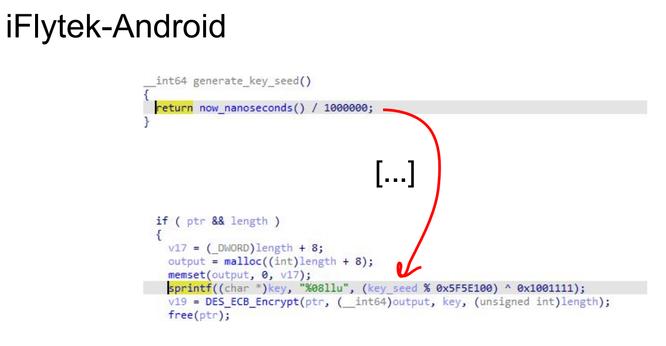
Next up, 'The widespread popularity of insecure proprietary network encryption in the Android ecosystem', presented by Mona Wang
#realworldcrypto
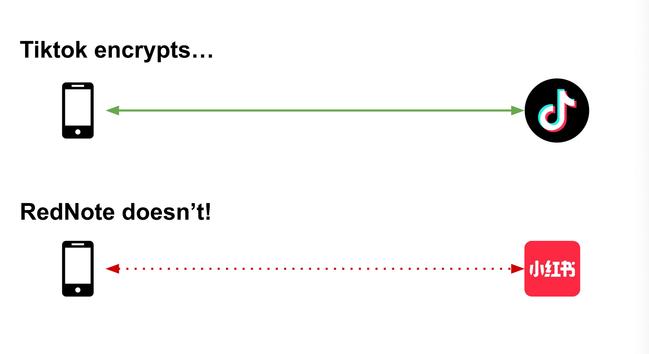
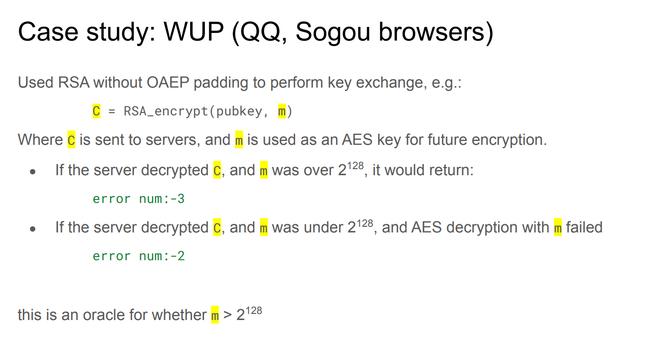
Chinese mobile apps are encrypting way less
ieeexplore.ieee.org/document/110...
#realworldcrypto
WireWatch: Measuring the Secur...
WireWatch: Measuring the Secur...
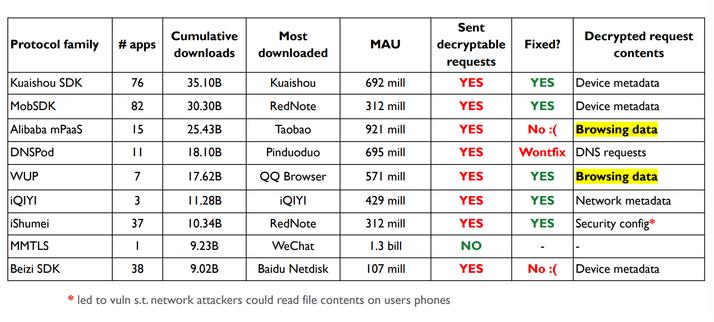
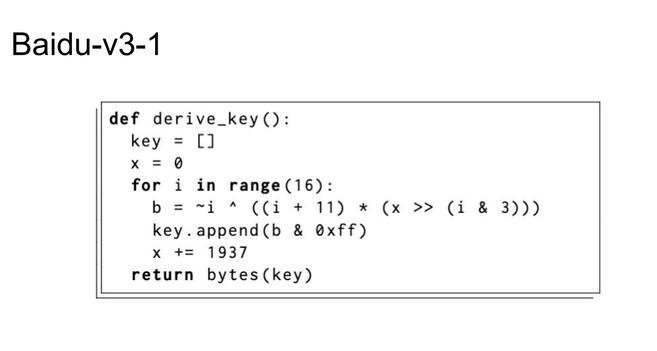
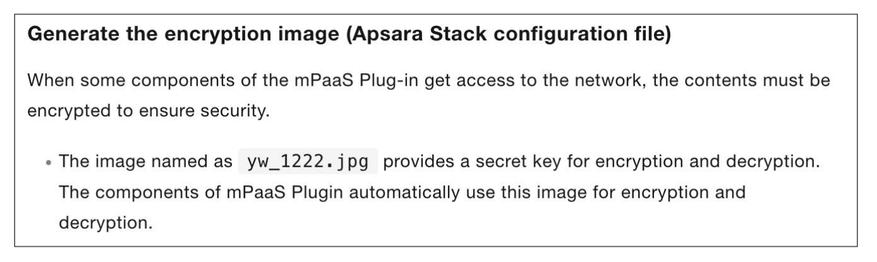
So broken!
#realworldcrypto
Keyboards, browsers, analytics, ads, device data, etc— all fucked
#realworldcrypto
These look like fun CTFs
#realworldcrypto
"I can't sleep, knowing what I've seen"
#realworldcrypto
lol wtf
#realworldcrypto
None of the schemes tried to provide cryptographic integrity or
authenticity, except for MMTLS
#realworldcrypto
Are these backdoors?????? (No)
#realworldcrypto