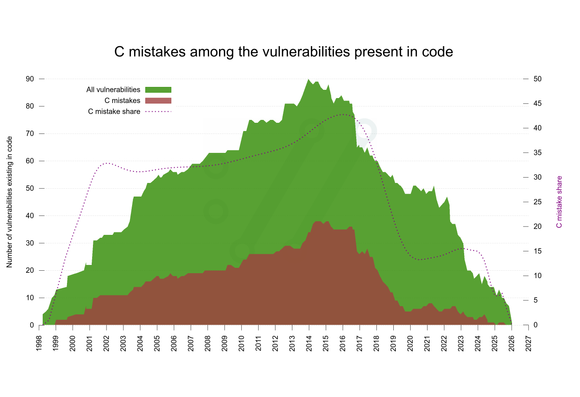
Looking back at all (now) published vulnerabilities in #curl that were present in code from 2020 until now, at no point in those years was the share of "C mistakes" higher than 15% of all vulns.
Through all years, the C mistake share of all vulnerabilities in #curl was never above 45% at any single point in history.