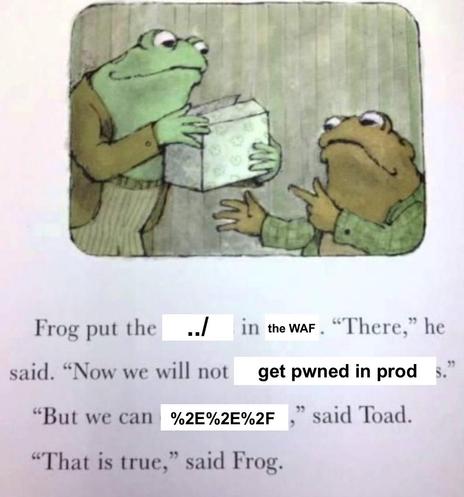
Can someone please explain to me, why directory traversal still is an attack vector in this day and age?
It was among the first things in medias res infosec, some – oh my – 30 years ago.
We've developed so many tools and defenses against this BS that it really, really shouldn't be a problem anymore.
- Having people following guides online from strangers without security first.
- Asking ChatGPT without prompting correctly for proper perms.
- Hobbyists figuring it out as they go.
lomg story short:
The Government-Director, reading payrol of IT-dep. Calling HR: What the hell!, DevOp salary near me? Fire him!
(Disclaimer:
thats only true in Government not in Industry et al)
Not surprising where open WAF to find.
😇
@i0null last time I reported a path traversal two things happened:
@qgustavor @i0null regarding the 2. point:
The company in question has probably more problems than you would like to work with so that's a bullet dodged.
 domenuk
domenuk