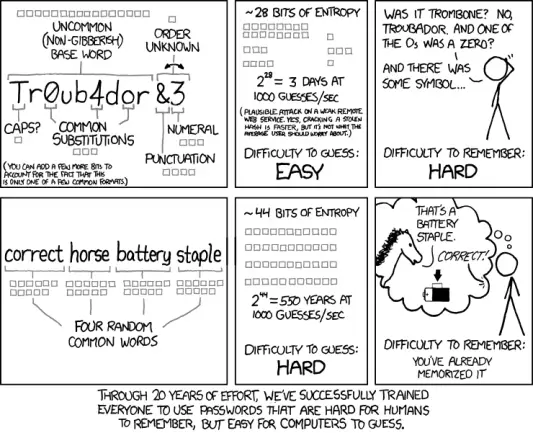
Passwords. We all hear “make them strong,” but here’s the real deal: SIZE matters.
A longer password isn’t just better; it’s exponentially harder to crack.
Upgrade your security and better protect your digital identity:
✅️ Create strong and unique passwords.
✅️ Store them in a password manager.
Learn more here: https://tuta.com/blog/minimum-password-length