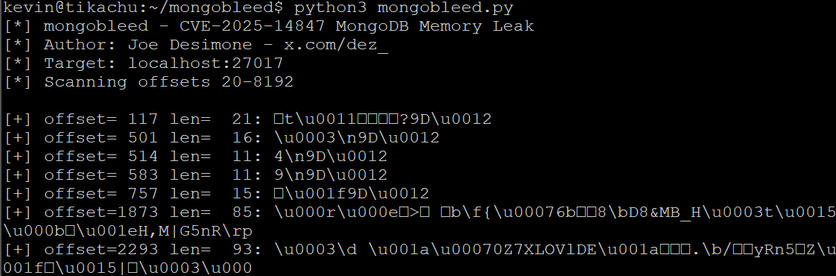
Merry Christmas to everybody, except that dude who works for Elastic, who decided to drop an unauthenticated exploit for MongoDB on Christmas Day, that leaks memory and automates harvesting secrets (e.g. database passwords)
CVE-2025-14847 aka MongoBleed
Exp: https://github.com/joe-desimone/mongobleed/blob/main/mongobleed.py
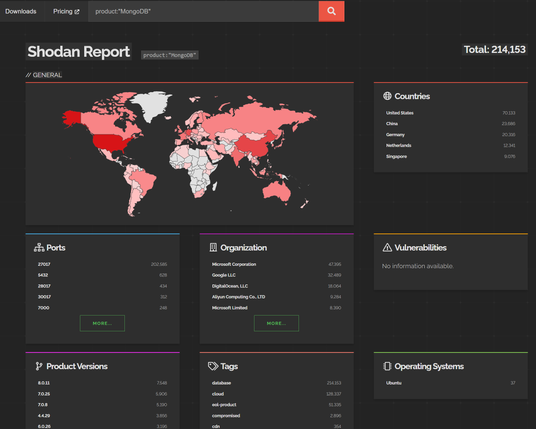
This one is incredibly widely internet facing and will very likely see mass exploitation and impactful incidents
Impacts every MongoDB version going back a decade.
Shodan dork: product:"MongoDB"