For a new project, I started to dig into older threat reports, like for example, "The ProjectSauron APT" from 2016. [1]
The interesting thing about these old reports is that you see techniques mentioned before that are still used 10 years later.
"ProjectSauron usually registers its persistence module on domain controllers as a Windows LSA (Local System Authority) password filter. This feature is typically used by system administrators to enforce password policies and validate new passwords to match specific requirements, such as length and complexity. This way, the ProjectSauron passive backdoor module starts every time any domain, local user, or administrator logs in or changes a password, and promptly harvests the passwords in plaintext."
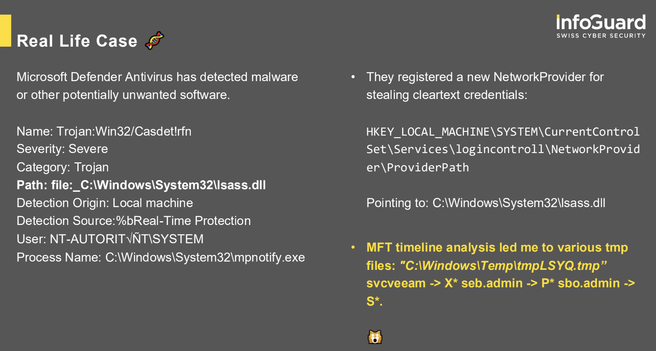
There are various ways to register such "password filters", but the screenshot is from a recent case (and from one of my presentations) in which the attacker registered a new NetworkProvider to steal cleartext credentials. Techniques which are 10+ years old are still working and (mis-)used by attackers.. 🤷