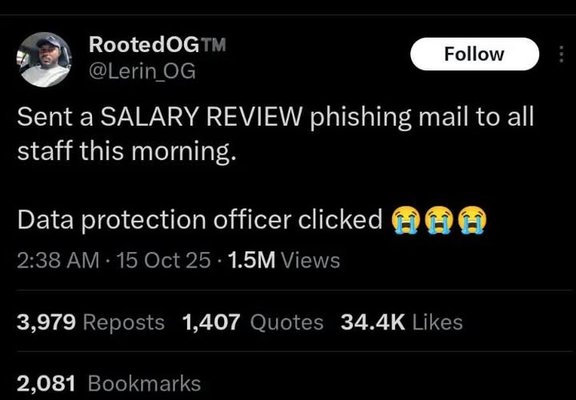
LOL
LOL
Back in the day when I was a Unix/Linux sysadmin guy for a medium sized enterprise, I sent a similar email asking people not to ever share their SSH or API keys with anyone, even if they claimed to be from the IT group. Guess what? Many replied and shared those keys. These were all developers. That day, I realized people have no chance. Now we see people install an app on their phone because someone claims to be calling from a bank or government and they lose their life savings. It is messed up
@nixCraft this is exactly why I think forcing companies like Apple to open up needs to be accompanied by consumer protections. Otherwise people WILL be taken advantage of
@nixCraft You now the thousand things I say next, ja?
@nixCraft lmfao
everywhere else:
sent: give me your api key
received: no way, scammer
meanwhile at your prev enterprise
sent: dont share your keys
replied: okay, here is my key
If I've learned anything from IT its that there is a wild difference in tech literacy and security literacy.
I just got done spending two weeks learning enough JavaScript to be able to read our developers code because the security guy found out they were trying to set prices on the client side.
It tooK two weeks of explaining to the Devs, the B2B team, and the CIO and CMO why this is ACTUALLY REALLY BAD to let CUSTOMERS set PRICES.
@nixCraft OpenSSH supports U2F keys since version 8.2. Impossible to clone or share.
@nixCraft About five people in a local LUG care about security. The rest of the world installs and accesses stuff with a total lack of concern.
@nixCraft
I believe the writer Frank Herbert said, The danger of technology is not in the technology. The danger of technology is the ability to do something without thinking.
I believe the writer Frank Herbert said, The danger of technology is not in the technology. The danger of technology is the ability to do something without thinking.
@nixCraft that's one way to find out if you should hire a data protection officer
@nixCraft not really lol, no :(
@nixCraft and you think it is ethical to announce this publicly, because no one knows who you work for?
bad publishing on your side.
bad publishing on your side.
@nixCraft Security jobs in 2025:
@nixCraft a virus ran wild in a company inspite of email filtering.
Turned out, the filter did indeed work.
But the admin had opened the flagged attachment to see what‘s inside.
@icing ah, yes curiosity killed the cat.
@nixCraft
I once got an obviously phishy email from work, and I was hovering over a link to see which phish trap site they were using.
And I accidentally tapped on my trackpad.
Damn it.
@nixCraft Everyone who clicked should be given a raise, especially the DPO.
@nixCraft I know I shouldn't...but maybe I need too
@nixCraft
Human brain, the greatest security vulnerability known to man
Human brain, the greatest security vulnerability known to man
@nixCraft yeah, sounds about right. HR clicked on our last phishing test and provided credentials. All of them.
Time before that, all of our privacy officers did.
Endusers who are the least tech savvy called or mailed us with questions if it was legit.
Classic 😅
@nixCraft At my last job, HR sent out an email about expecting the annual bonus gift selection email to arrive that would contain a link to a third party site that we use for selecting the gift. An hour later, IT sent out a phishing test email saying it was the gift selection email that we were told to expect to receive. That was a nasty phish. I am not sure if it was a set-up between HR and IT, or someone in IT taking advantage of the HR email when they saw it. Link shorteners suck!