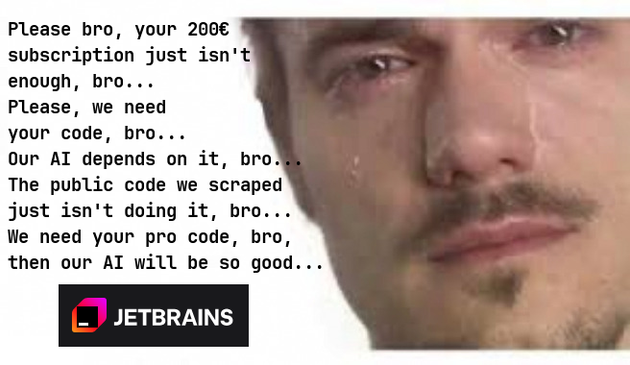
New Jetbrains Update Dropped
Doesn’t anyone else use things like OpenSnitch to audit all outgoing connections? I block all phone homes until something breaks, then investigate.
If you are trapped on Windows for some corporate reason, there is SimpleWall.
We’re friends, and friends don’t let friends let apps phone home.
Thanks for that suggestion, I had a passing thought a while back I should look into something like this.
Any problems in your experience? I imagine apps will fail if you’re slow to approve the outbound connection and something times out, so I get all of that, looking more for broader issues this might cause? Specifically wondering about the docker containers I run, all the development nonsense.
But aside from plugins, whenever I see people using VS Code/-ium, I wonder why they keep raving about it. It just looks like a bogstandard editor with LSP support to me. And Microsoft may have gotten that LSP ball rolling, but it’s supported in lots of editors now…
VScode is certainly a heck of a lot easier to get LSPs working than e.g. vim.
If someone made it actually easy to set up neovim with lsp support that works as well as with vscode, there’d be no reason to give Microsoft any attention at all
Is the LSP support a plugin in Neo-/Vim ?
In Kate, you just install the LSP server, which is typically as simple as apt install marksman and then Kate will automatically start it when it encounters an appropriate file.
Kate also has a Vi Mode, if that’s what you’re looking for. ¯\_(ツ)_/¯
Here is the default configuration: invent.kde.org/utilities/kate/-/…/settings.json
If you do need more LSP servers or a different one for a language, you can specify your own custom configuration in the same format.
vim.lsp.enable(“server-name”) command, which you just put in your config and the Neovim will start the LSP when you open a relevant file.
Ah, I guess that makes sense. Kate automatically detects available LSP server executables but then prompts you before starting them for the first time, in case you did not install that and it’s malware, or I guess, in case you just placed a script there which happened to be called the same, but would be very bad to run.
Neovim could theoretically do that, too, but then you need a way to block executables, so that it stops prompting you every time, which you’d probably want in a separate config file.
So, it’s definitely a simpler solution and perhaps moreso what one would expect from a TUI editor, for you to just list the ones to run in the config file.
Neovim has something better - there is a plugin that installs the servers for you - github.com/mason-org/mason.nvim - and then you can just use the servers that plugin has installed (which should be more trustworthy because you just need to trust the plugin and not some random executable)
There is also github.com/mason-org/mason-lspconfig.nvim which bridges the two and automatically enables servers that were installed via Mason.
This was one of my biggest issues, but I did manage to succesfully switch to nvim few months ago, by installing ideavim into Rider, vscode-vim into vscode (so I can’t easily escape it when I get lazy), but most importantly - setting LazyVim as my default editor, which has been a lifesaver.
It has a pretty good LazyExtras interface for easily installing a ton of plugins, almost for every language. You just open the LazyVim menu, select a language you want, and it installs LSPs, debuggers and whatnot you may need for it. It’s probably using the nvim-lspconfig mentioned in other comments, but it has been pretty seamless.
But any other pre-made nvim config will work, this one is just more approachable than someone’s random plugin list.
Anyone new to these tools will be horrified at how aggressively Windows violates tries to violate your privacy with unnecessary data collection, phone-homes, etc.
Linux is galaxies better in that regard. I still don’t want anything making any connections without my explicit knowledge and consent though, and there are lots of packages and applications that try to unnecessarily exfiltrate data without asking. If you aren’t using an active firewall, you are leaking.
NotMyProblemException.
I second OpenSnitch. It’s the most annoying program i run, but the control it gives you over your outbound connections is so worth it from a security and privacy standpoint.
Once you start and run this you get to truly see how many different URLs are loaded when visiting just one website
Since then I run SimpleWall and I highly recommend everyone else do the same. It’s annoying at the beginning but annoyance turns into peace of mind when you known nothing, not even built-in Windows processes can phone home without you knowing.