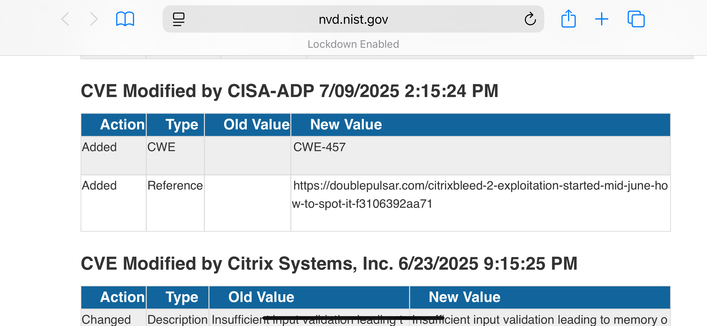
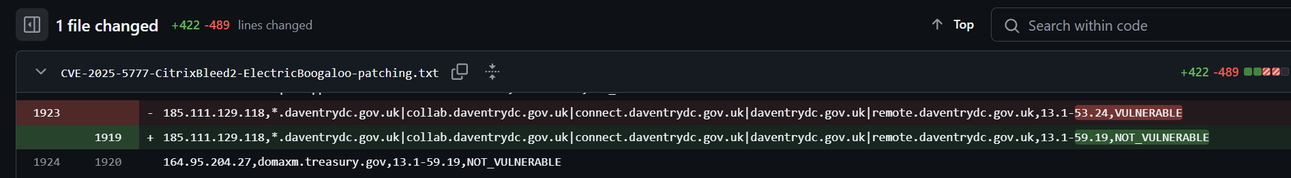
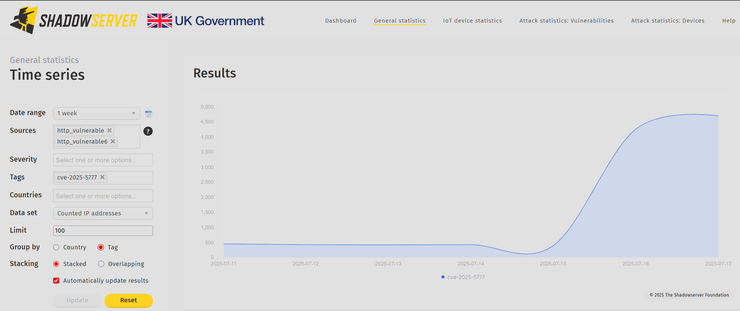
I believe Citrix may have made a mistake in the patching instructions for CitrixBleed2 aka CVE-2025-5777.
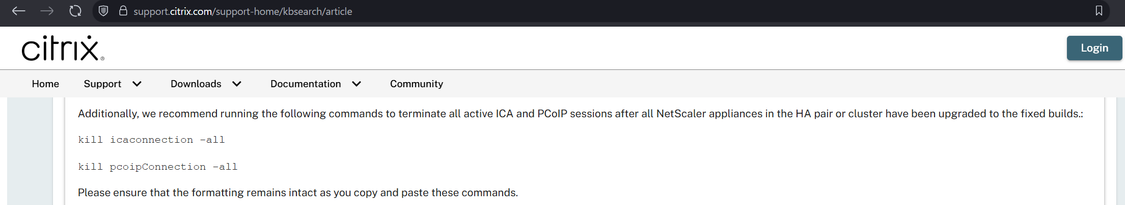
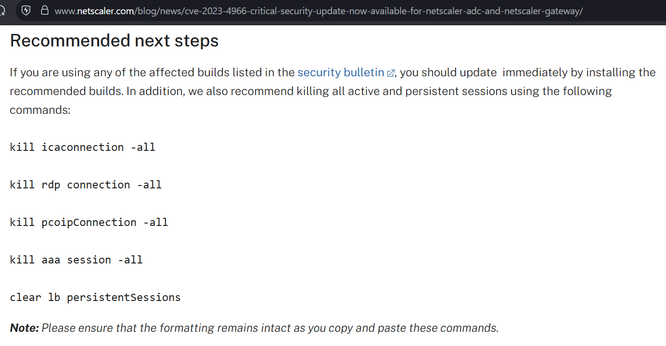
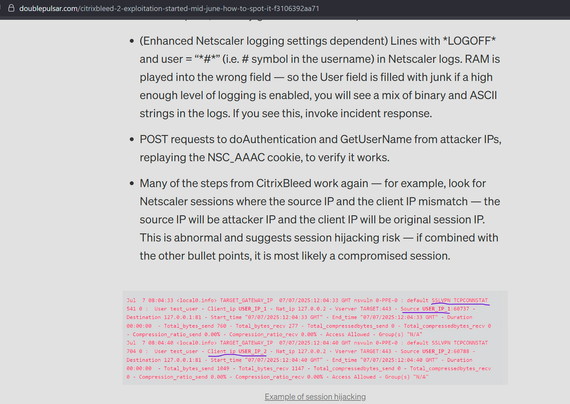
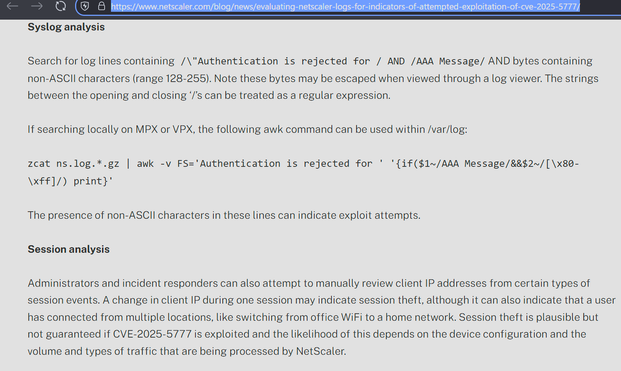
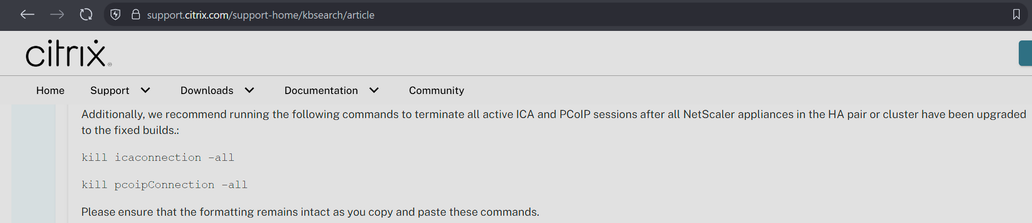
They say to do the instructions on the left, but they appear to have missed other session types (e.g. AAA) which have session cookies that can be stolen and replayed with CitrixBleed2. On the right is the CitrixBleed1 instructions.
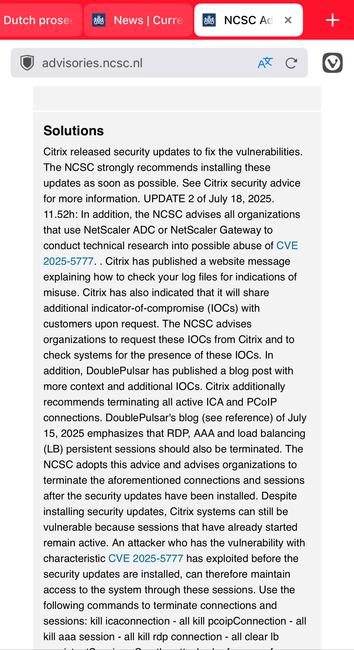
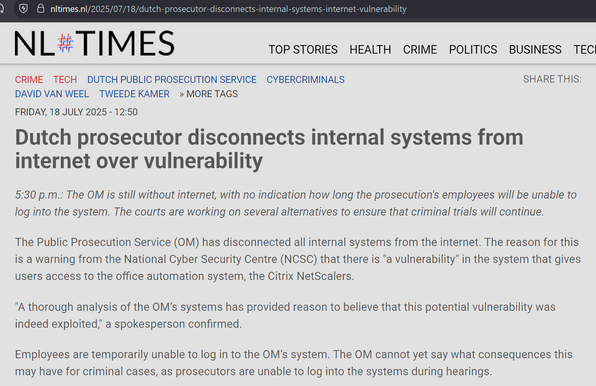
The net impact is, if you patched but a threat actor already took system memory, they can still reuse prior sessions.
Tell anybody you know at Citrix.