Malicious javascript compromise on npmjs.com
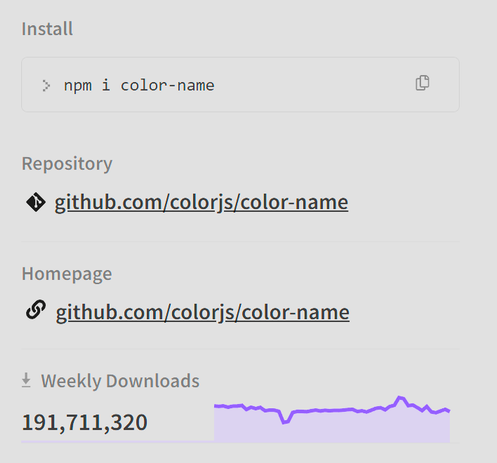
These packages, about a billion downloads prior
supports-hyperlinks
chalk-template
simple-swizzle
slice-ansi
error-ex
is-arrayish
wrap-ansi
backslash
color-string
color-convert
color
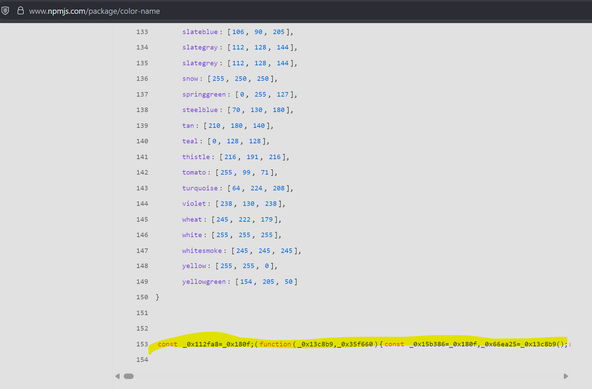
color-name
Thread follows.