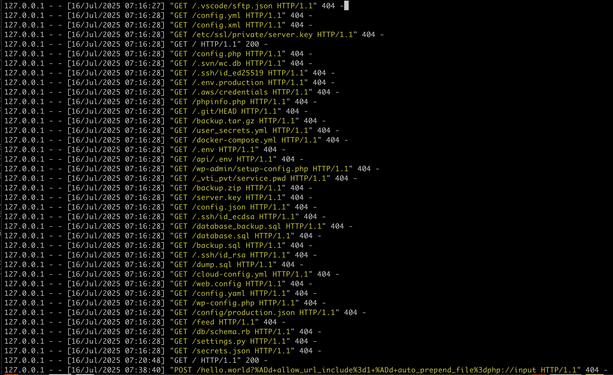
and what you can take away from this log is that the reason they are blasting the entire internet, every webserver with these requests - most of which are 'im gonna hit myself in the face with a brick now' level of bad from a config/dev/admin perspective - is squarely because it has worked for them enough times that they feel spraying the internet will nab them more.
look.
just look at the shit they're collecting and how easily theyre doing it.
this is because docker
this is because k8s
this is because everywhere has gone "DX" - or "optimizing for the developer experience above all else, at the cost of everyone else. "
make things as easy as possible for the devs/devops, we dont care how bad the security becomes, how many layers of abstraction get installed, how many dozen new js frameworks appear this afternoon, how public the data is, how bad the architecture is - burn the building down
just make sure the devs are comfy