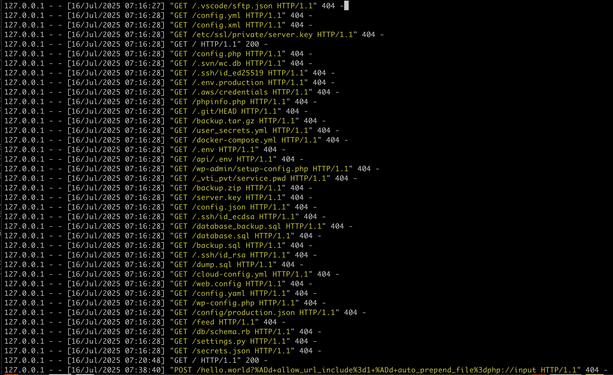
and what you can take away from this log is that the reason they are blasting the entire internet, every webserver with these requests - most of which are 'im gonna hit myself in the face with a brick now' level of bad from a config/dev/admin perspective - is squarely because it has worked for them enough times that they feel spraying the internet will nab them more.
look.
just look at the shit they're collecting and how easily theyre doing it.
this is because docker
this is because k8s
this is because everywhere has gone "DX" - or "optimizing for the developer experience above all else, at the cost of everyone else. "
make things as easy as possible for the devs/devops, we dont care how bad the security becomes, how many layers of abstraction get installed, how many dozen new js frameworks appear this afternoon, how public the data is, how bad the architecture is - burn the building down
just make sure the devs are comfy
"this is because docker
this is because k8s"
I'm curious to hear more about this take. I'm only a hobbyist at this point, but I run some docker services on my local network, nothing (to my knowledge) exposed to WAN or ports forwarded. Surely this can't be *mostly* docker and DX's fault that the internet is like this, can it?
The reason I ask is because I care about my services and network being secure, and in the future I would like to host public web servers, though probably not from my home network. Inevitably there will be something I'll miss when embarking on a project like that, but I'm wondering if there's a takeaway I'm missing from these posts aside from avoiding abstraction as much as possible when designing web services.
@crocodisle i have seen the inside of probably 30 companies worth of k8s infrastructures.
ive seen things.
@crocodisle if you want free advice:
- if you want to host a thing and you want that thing to be public, do not host it inside of docker or k8s.
- there are many many reasons why, and i dont want to turn this into a 300 post long thread
- whoever decided that all the secrets need to be stored in env vars or in files called .env should not be allowed to touch computers anymore
- do your coding/building behind a firewall
- push static content to 'a host'
- do not run docker or k8s on that host.
@Viss @crocodisle so far all of your reasoning has zero to do with the infrastructure or deployment practice of choice. Its all poor dev practices and repository layout. There are ignore files for this. There are rule enforcement engines and free scanners like rego and trivy to prevent these mistakes.
Its just a product of the VC driven rat race in Tech these days. No one takes time because they feel they don't have time, or the work gets slapped into a tech debt epic and deprioritized in favour of company goals.
Put it on the most tried and true tech possible and without the time to wisely layout code and its delivery, and you'll get someone's local dev files in production... Every. Damn. Time.
if you let people buy cars with no seatbelts or airbags, they're gonna buy cars with no seatbelts or airbags.
telling people to not buy the cars that were sold without seatbelts or airbags is good advice, even if you can add them on after the fact.
the people who add seatbelts and airbags into their cars that didnt come with them are in the tiiiiiiiny minority, while practically everyone else is screaming down the freeway at 100 and cant stop.
@Routhinator @crocodisle of course you can do it better. of course you can harden things.
the problem is shit like docker and k8s were written by people who expressly dont do that. then they hamfistedly tried to staple that shit on after the fact.
and these logs are evidence that its such a prevalent issue that scanning the entire internet loudly keeps dishing out gold for attackers, so they keep doing it.
if it didnt work, and people hardened their shit, attackers wouldnt be scanning