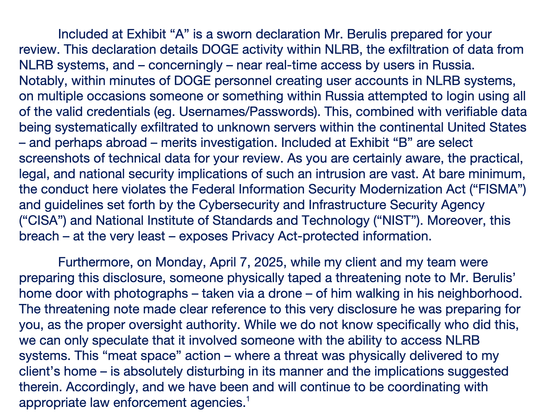
🧵 THREAD: A federal whistleblower just dropped one of the most disturbing cybersecurity disclosures I’ve ever read.
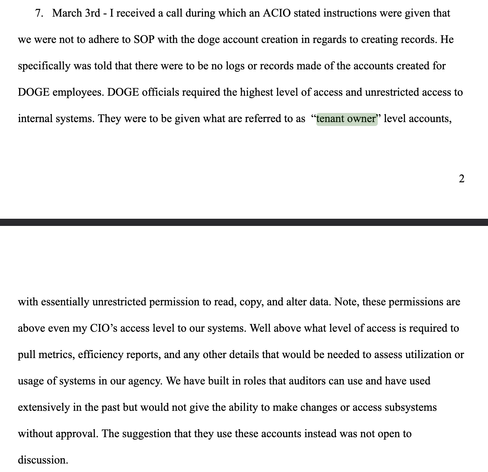
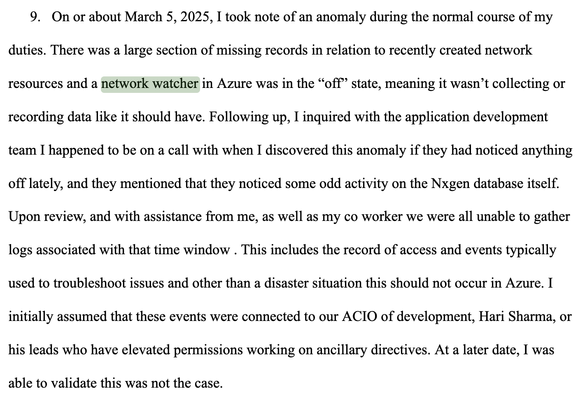
He's saying DOGE came in, data went out, and Russians started attempting logins with new valid DOGE passwords
Media's coverage wasn't detailed enough so I dug into his testimony: